The MacValley blog
![]()
Welcome to the MacValley blog, your first stop for all the latest MacValley news and views.
|
The MacValley blog Editor: Tom Briant
|
Labels used in posts
|
To search the blog posts please use the box below
Sunday, February 28, 2016
I Review the Dell P2416D 24" monitor
To begin with, I have bad eyes. I need a strong prescription. What could I do to help at home?
I own a late 2011 Mac Mini. I had thought of buying a 4K monitor for it, but found that this model only supports 2560 x 1440 through the Mini Display/Thunderbolt port and 1920 x 1200 through the HDMI port. So I went shopping for an appropriate monitor.
I found the Dell P2416D at Fry’s Electronics in Woodland Hills for $299.95. It comes with three interfaces; full-size Display Port, HDMI and VGA. It also has a 4-port USB 2.0 hub built in.
I assembled the monitor at home, put it on the desk, plugged in the Display Port to Mini Display Port cable that I bought at Fry’s; turned it on, and voila! A Beautiful 2560 x 1440 desktop appeared on screen. I didn’t need to install drivers or fiddle with the controls. It just worked.
The monitor includes a 4 port USB 2.0 monitor. Dell does include a USB A-B cable to hook it up to your Mac or PC. The connections are in the back of the monitor, out of sight and inconvenient for quick changes. Set it up for the long term for your keyboard and mouse. If you need ports for quick access, buy a separate USB hub to plug into the computer itself. The monitor’s hub shuts down when you turn off the monitor. It’s not a powered hub, so don’t plug hard drives that derive their power from the USB port.
Dell includes documentation and Windows software on a companion CD. You read the documentation through your Web browser. I found it clear and to the point. I could see the illustrations and interpret them with no problems. Kudos to Dell on this part, too.
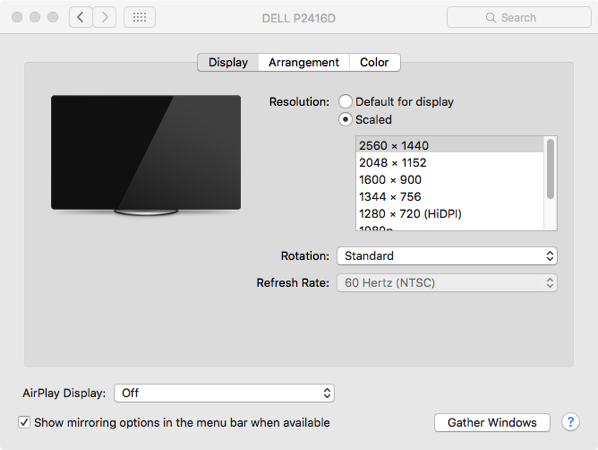
One feature of this monitor is that you can physically rotate the monitor 90 degrees to give you a portrait orientation, as opposed to the usual landscape. As I said, Dell didn’t include drivers for the Mac to automatically change the screen orientation with the right Dell video card. You just go through the Display Preference Pane ( to orient your display as desired.
Changing the display’s orientation does not change the app’s orientation on the screen. I just tried with Safari. You graphics users can tell me about your experiences in the comments.
Finally, the best part. As I wrote above, I have bad eyes. Through the Display Preference Pane, you can change the resolution of the monitor. I changed it from 2560 x 1440 to ¼ of the resolution, 1280 x 720 Hi DPI.
I found it easy to switch between the two resolutions through the Display Preference Pane. I didn’t need to logout or reboot my Mac Mini. The screen just flashed briefly, not disrupting the music from iTunes.
Fry’s has this monitor for $299.95. The Dell Website has it for $329. I suggest if you want to try Fry’s that you order it on-line . I was lucky when I walked in the door, as Fry’s in Woodland Hills only had 1 of these in stock.
Summary
If you have tired eyes and your Mac or PC cannot work with a 4K or 5K monitor, I recommend the Dell P2416D for quick relief. The interface options can meet just about every computer on the market today; Display Port/HDMI/VGA. The monitor worked with my Mac out of the box.
Dell P2416D 24” monitor with Quad HD display
Comes with monitor, stand allowing for physical rotation of display, power cable, Display Port to Display Port cable, and USB 2.0 A-B cable. You’ll need a separate Display Port to Mini Display Port cable to work with a Mac. Documentation and Windows XP/7/8 drivers on accompanying CD.
$299.95 at Fry’s
$329 at Dell.com
Senior Correspondent Arnold Woodworth's Weekly Web Wrap-up for February 28,2016
A 23-year-old man in Alabama has become the latest person to follow a phone-tracking app all the way to his grave.
http://www.usatoday.com/story/news/2016/02/23/man-killed-after-tracking-down-his-stolen-iphone-newser/80795194/
This case is about much more than a single phone or a single investigation, so when we received the government’s order we knew we had to speak out. At stake is the data security of hundreds of millions of law-abiding people, and setting a dangerous precedent that threatens everyone’s civil liberties.
As you know, we use encryption to protect our customers — whose data is under siege. We work hard to improve security with every software release because the threats are becoming more frequent and more sophisticated all the time.
Some advocates of the government’s order want us to roll back data protections to iOS 7, which we released in September 2013. Starting with iOS 8, we began encrypting data in a way that not even the iPhone itself can read without the user’s passcode, so if it is lost or stolen, our personal data, conversations, financial and health information are far more secure. We all know that turning back the clock on that progress would be a terrible idea.
The investigators can't protect the iPhone users who then would be open to attack, but they don't see that as a problem, because they would not be held accountable for it, and they are missioned to gain access to one particular phone.
If we went down a list of the folks who were most likely to be compromised, it would include the First Family, many in Congress, and likely not an insignificant number of FBI families. Yet this path still appears reasonable to the FBI, because the folks who would benefit would not be held accountable for the resulting problems.
Apple is on the other side. It won't sell more phones if that one iPhone is compromised, but if all iPhones are made insecure as a result, its sales will crater.
And they're taking on more tasks all the time; increasingly personal tasks at that. They are handling our financial transactions, monitoring our bodies, and even conversing with us using real language. They are taking over the ways we interact our vehicles, and soon enough will take complete control of them.
The line between software and meatware will only continue to blur. I have little reason to doubt that the scorching hot wearables space will—in the not crazy future—give way to implantables. That may seem like a sci-fi step too far for many, but mark my words, this is a thing that will happen.
The first time someone is injured when a self-driving car is commandeered by a bored hacker in Ukraine, people will stop using that brand of self-driving car. The same goes for the first time someone breaks into the fitness tracker being monitored by your doctor; the supposedly secure wireless payment platform; or yes, the implantable device you can't easily remove.
Hackers and bad players have always been with the Internet. As technology drags both our minds and bodies further into The Matrix, consumers will only want to do business with companies that take the security of our most intimate selves very seriously.
After Apple’s lawyers revealed that the agency is trying to gain access to about a dozen devices, it’s becoming increasingly clear why the government chose to take the San Bernardino case public.
The FBI may be winning the public-relations battle it’s fighting with Apple alongside the ongoing legal conflicts. According to a poll that Pew Research conducted over the weekend, most Americans think Apple should honor the FBI’s request to unlock Farook’s iPhone. But now, Apple has a new arrow in its quiver: It can show that helping the FBI in California will have far-reaching consequences.
"In this specific case, I'm trending toward the government, but I've got to tell you in general I oppose the government's effort, personified by FBI Director Jim Comey,” Hayden said.
"There’s always a risk that your iPhone can be stolen, and the people who stole it can use the data, your private photos, etc to blackmail you," he said. Forcing Apple to build tools to defeat its own security methods would set a dangerous precedent, he added.
There is no reliable way to build a pathway to undermine Apple’s security that will only let in good guys. And once it has built this path, there is no way that the law will limit Apple to using it on a single phone. Neither the technology nor the law supports this. As security expert Bruce Schneier said, either we all have security or none of us does.
This is about all of our safety and resisting government overreach. These are hard battles to fight—we know. We [the EFF] have been fighting them for many years.
https://www.eff.org/deeplinks/2016/02/eff-apples-shareholders-meeting-statement-support
While it defies U.S. government, Apple abides by China's orders — and reaps big rewards
Apple Inc. has come out swinging in its pitched battle with the government on its home turf.
But when it comes to its second-largest market, China, the Cupertino, Calif., company has been far more accommodating.
Since the iPhone was officially introduced in China seven years ago, Apple has overcome a national security backlash there and has censored apps that wouldn't pass muster with Chinese authorities. It has moved local user data onto servers operated by the state-owned China Telecom and submits to security audits by Chinese authorities.
The approach contrasts with Apple's defiant stance against the FBI, which is heaping pressure on the company to decrypt an iPhone that belonged to San Bernardino shooter Syed Rizwan Farook.
The environment will get even tougher, Apple says, if the FBI prevails in seeking a so-called backdoor to Farook's phone. That could set a precedent for China's authoritarian leaders to demand the same in a country where Apple has never publicly defied orders.
"What's driving this is Apple's desire to persuade the global market, and particularly the China market, that the FBI can't just stroll in and ask for data," said James Lewis, senior fellow at the Center for Strategic and International Studies in Washington. "I can't imagine the Chinese would tolerate end-to-end encryption or a refusal to cooperate with their police, particularly in a terrorism case.”
Apple ... all data on the servers were encrypted and inaccessible to China Telecom.
China is introducing security laws that are so vaguely worded some fear it will require technology companies to provide source codes and backdoors for market access.
The ambiguity of China's security laws are designed to promote self-censorship.
http://www.latimes.com/business/technology/la-fi-apple-china-20160226-story.html
Lawyer For Apple: 'What In The Law Requires Us To Redesign The iPhone?’
"What in the law requires us to redesign the iPhone, to rewrite code, to provide an Achilles' heel in the iPhone?” Ted Olson said. "It was designed to protect the secrecy and privacy of individuals who use the iPhone."
Olson said Apple has cooperated "in every way in every federal or state criminal investigation, up to the point that the law permits it" — but that writing software for the iPhone to make it less secure crosses the line.
http://www.npr.org/sections/thetwo-way/2016/02/26/468228567/lawyer-for-apple-what-in-the-law-requires-us-to-redesign-the-iphone
Here’s the text of Apple’s latest court filing
http://www.scribd.com/doc/300522240/Motion-to-Vacate-Brief-and-Supporting-Declarations
Really understanding Apple's legal brief in the FBI case
Congress should get involved
The fight between Apple and the FBI over the security protections on the San Bernadino iPhone has been fierce for the past few weeks, but it’s mostly been a PR battle thus far. From a legal and procedural standpoint, only two things had actually happened until yesterday: the FBI filed a motion to compel Apple to help it bypass security restrictions on the phone, and a magistrate judge ordered the company to comply. But yesterday Apple filed a motion to vacate judge Sherri Pym’s order, which lays bare the company’s actual legal argument against building a special one-off version of iOS that would allow the FBI to unlock the phone with a brute-force attack on its passcode.
the actual substantive issue in this case is pretty simple: Does the government have the authority to order Apple to help unlock the phone based on statute or precedent? That’s the only question anyone’s trying to answer, since almost all the other facts in the case break decisively in the government’s favor: the government owned the phone, there’s a warrant, the guy was a terrorist asshole, etc., etc., etc. Apple doesn’t even really bring any of that up. The entire brief is focused on whether the government has the power to make Apple help law enforcement.
Lots of legal analysis here that is not in any other article of this issue.
http://www.theverge.com/2016/2/26/11120760/apple-vs-fbi-legal-brief-explained
Here's what it would cost Apple to help the FBI hack an iPhone
(or so some non-Apple experts claim)
This nightmare dream team of employees working full-time to create a big back door -- something CEO Tim Cook calls a "cancer" -- would only cost the company $100,939.
Apple makes clear that creating this "cancerous" code poses a huge risk for the company.
To keep this hack from ever leaving Apple's premises, Apple would probably house its "hacking department" in a new, highly-fortified containment lab. In a court declaration, Apple lawyer Lisa Olle said the company would "likely" build "one or two secure facilities" similar to a "Sensitive Compartmented Information Facility.”
Think: top-secret CIA compound.
Apple didn't provide any cost estimates, so CNNMoney consulted with licensed experts who build SCIFs. They said it would cost $25 million to build a new one. For two? That's $50 million.
Apple's really fighting this case on civil rights grounds. It claims the government can't be "conscripted... to do the government's bidding" and make everyone's iPhone "crippled and insecure."
http://money.cnn.com/2016/02/26/technology/apple-iphone-fbi-hack-cost/
At first glance, the issue seems simple: Why shouldn’t law enforcement have access to information that could help us hunt down other terrorists or even to help prevent other terrorist attacks in the future?
But this simplification overlooks the reason why companies have built their systems so securely to begin with: namely, to prevent criminals, terrorists and hackers from gaining access to our private and sensitive information. It’s a huge technological breakthrough that engineers are able to build systems so secure that even their own architects cannot break into them. And it’s why major players in the tech industry—from Facebook and Twitter to Microsoft and Google—are lining up to support Apple’s stance.
As Americans are increasingly living their lives online, it’s now become just as important for people to be able to secure their phones, laptops, credit card numbers, and accounts from intruders as it is to secure their homes.
Hackers have already stolen huge amounts of personal information (credit card numbers, social security numbers, bank account numbers) from both corporations and the Government.
Forcing Apple to manufacture new security vulnerabilities into its phones’ operating system in order to give the government access paves the way for these kinds of breaches to become all the more common. But even more alarming are the implications this decision would have for the online security of Americans for generations.
No one would say that Apple should obstruct justice or intentionally impede law enforcement’s attempts to bring perpetrators of heinous acts of violence to justice. But a company also shouldn’t be forced to deliberately weaken the integrity of their own products and subject millions of customers to security vulnerabilities in order to do so.
Whether tech companies like Apple can be forced to undermine their own products and whether they will have to leave a backdoor open for government—and whoever else may find it—in their products is currently a question left to the courts. But as Congress begins contemplating revisions to the 1789 statue upon which this court order is built, lawmakers must be sure to protect citizens’ right to privacy and preserve the integrity of the online security protocols that help keep us all safe.
http://www.wired.com/2016/02/forcing-apple-hack-iphone-sets-dangerous-precedent/
Apple’s battle with the FBI is being talked about as a defining moment for privacy. And it is. But the real reason why is obscured by both sides’ rhetoric.
Apple says what makes this case different—a precedent that, once set, will bend tech firms to the government’s every future whim.
Yet the government’s claim is disingenuous too. It implies that everything is a continuum and there are no matters of principle.
The reality, however, is that everything we now consider a matter of principle—from the ban on insider trading all the way back to “thou shalt not kill”—was once a line drawn in the sand, and only over time became a mighty barrier. Principles don’t get made until someone says “enough.”
Apple has now said “enough.” Other tech companies are joining in. Principles aren’t enshrined because of a legal wrangle over a technological quirk. They’re enshrined because someone chooses to stand and fight for them.
http://qz.com/626710/the-apple-fbi-showdown-is-about-something-more-basic-than-software-and-laws/
Verizon Wireless, the largest mobile carrier in the United States, has strongly — and rather unexpectedly — stood up in support of Apple in its legal showdown with the FBI. In a statement, CEO Lowell McAdam said "Verizon is committed to protecting customer privacy and one of the tools for protecting that privacy is encryption." According to the chief executive, Verizon supports "availability of strong encryption with no back doors."
And just like Apple's Tim Cook, McAdam is pushing for a resolution to be decided by Congress rather than having the outcome determined by a single judge or behind closed doors. "The case with Apple presents unique issues that should be addressed by Congress, not on an ad-hoc basis," McAdam said.
http://www.theverge.com/2016/2/25/11115540/verizon-backs-apple-against-fbi
Journalist Gets Hacked While Writing Apple-FBI Story
"That’s why this story is so important to everyone," says hacker, who was a fellow passenger on his flight.
When the flight took off, Steven Petrow’s stance on the matter was "I don’t really need to worry about online privacy," he writes for USA Today. "I’ve got nothing to hide. And who would want to know what I’m up to, anyway?" But by the time Petrow landed, he found out "in a chillingly personal way" just how much the outcome of the Apple-FBI battle matters to everyone. That’s because Petrow had been hacked mid-flight.
As the plane landed in Raleigh and Petrow got up to disembark, a passenger behind him revealed that he knew Petrow was a journalist and had just been working on the Apple-FBI story. The passenger even recited an email Petrow had received from a security expert back to him almost verbatim. This passenger knew all this information, he revealed, because he had hacked Petrow’s computer in-flight, as well as the computing devices of almost every other passenger on the plane.
"That’s how I know you’re interested in the Apple story," the hacker said. "Imagine if you had been doing a financial transaction."
The fact that Petrow was hacked mid-flight isn’t so shocking. It’s easy to get hacked on a public Wi-Fi network like Gogo. What was most shocking to Petrow was how this in-flight hacking clarified his stance on the Apple-FBI battle.
"My mind raced: What about my health records? My legal documents? My Facebook messages? That’s why this story is so important to everyone. It’s about everyone’s privacy," he writes. "I may have been wearing my jacket, but I felt as exposed as if I’d been stark naked."
Now just imagine what would happen if a backdoor into an iPhone was as easy to get through as the backdoor on a public Wi-Fi network.
"I realize now it's not that I have things that I need to hide but it is things that I expect to be kept private," Petrow said in a video speaking about the experience, "and it was disturbing and I have to say I’ve learned quite a bit."
http://www.fastcompany.com/3057138/fast-feed/journalist-gets-hacked-while-writing-apple-fbi-story
Apple hires developer behind encrypted messaging app Signal
Apple has just made a big — and timely — hire, recruiting a developer behind encrypted messaging app Signal, perhaps best known for being Edward Snowden's chat app of choice. The developer, Frederic Jacobs, confirmed the news on Twitter.
Signal has earned strong marks from privacy researchers, and the app became more widely known after some evangelizing by Snowden.
http://www.theverge.com/2016/2/26/11119314/apple-signal-developer-hire
Last year alone, the Defense Department was hacked. Using the NSA’s back door the Chinese walked off with 5.6 million fingerprints of critical personnel. The same back door was used to hack the Treasury Department on May 27th of last year in which millions of tax returns were stolen. And again, our most devastating hack as a nation was the Office of Personnel Management hack, in which 22 million sensitive files were stolen. The Chinese gained access through the Defense Department’s Juniper Systems and then using inter-operability with the Personnel Office, took what they wanted. Again, courtesy if the NSA’s back door.
Whatever gains the NSA has made through the use of their back door, it cannot possibly counterbalance the harm done to our nation by everyone else’s use of that same back door.
http://www.businessinsider.com/john-mcafee-nsa-back-door-gives-every-us-secret-to-enemies-2016-2
A hacker shows how you can take over security cameras and bank accounts with just an email
Great video.
If you dare a hacker to break into your accounts, chances are pretty high that you won't like the results.
http://www.techinsider.io/kevin-roose-hackers-2016-2
"The other main concern here is that the telematics system in the car is leaking all of my historic driving data," one security expert said in a blog post. "That's the details of every trip I've ever made in the car, including when I made it, how far I drove and even how efficiently I drove. This could easily be used to build up a profile of my driving habits, considering it goes back almost 2 years, and predict when I will be away from home. This kind of data should be collected and secured with the utmost respect for my privacy.”
https://www.openrightsgroup.org/
Raspberry Pi, the wildly popular — and crazily cheap — single-board computer used to promote computer science education and beloved by hobbyists.
The company launched its smallest and cheapest computer yet in November 2015:The Raspberry Pi Zero, which retails for just £3.30, or $5. Predictably, it sold out immediately.
https://www.raspberrypi.org
It’s easy enough to forget that the smartphone patent wars are still rumbling along.
Our problem is not this specific court ruling. Nor is it even the issue that was being battled over. The problem is the length of time it all took:
A 2014 verdict? But that’s two entire generations of phones ago! And that decision stems from the various suits originally filed in 2011. That’s five generations of this technology ago: and that’s what is wrong.
Again, our point here is not who is right and who is wrong, whether Apple should have beaten Samsung or vice versa. What we are concerned about is whether the patent system itself is fit for purpose. And it’s not entirely obvious that it is.
Inventing something is expensive. Copying an invention is generally cheap.
Why would you spend $ Billions if three weeks later anyone could copy your new drug?
Our answer is that we deliberately invent something called intellectual property. This comes in various forms, patents, copyright and trademarks.
Most patent disputes are not about firms copying each other’s inventions but about two companies discovering simultaneously the next step in an innovative process. Yet patent law can’t easily handle that type of situation.
This Apple Samsung case is showing us another fault with the system. Yes, we want to protect real innovation from copying. Simply because we think that produces more innovation over time and thus makes us all richer. And we also want to allow as much derivative innovation as doesn’t interfere with that aim. For, don’t forget, we’ve invented this intellectual property idea entirely out of thin air, in order to achieve a goal. That goal being to maximise innovation. It’s no use people shouting “Oi ! I invented that!”. We don’t care: this is not about justice and righteousness, it’s purely a utilitarian calculation about how to make the future richer.
That other fault being shown is that whatever system we use to decide upon such issues must be timely. Taking 5 years to decide (assuming that there won’t be yet more appeals) in a market with a new generation of devices at least every year simply isn’t timely.
http://www.forbes.com/sites/timworstall/2016/02/27/apple-samsung-patent-fight-shows-whats-still-wrong-with-our-patent-system/#171a61bb6af9
http://www.techinsider.io/360-degree-video-navy-fighter-launch-2016-2
https://www.facebook.com/FlyNavy/posts/10153416526668733
Sunday, February 21, 2016
Beginner's Column-How to change the desktop picture to something you want and where to get that picture
Making their Mac your Mac: what to know about customizing the desktop
Hello and welcome to my blog. I will offer you some tips and techniques on how to make the Mac you now own your Mac. Let Tim Cook decorate his Macs the way he wants. You should make your Mac your own. I’m here to give you some tips on the desktop wallpaper, the first thing you can fiddle with.
Lots of articles on this topic on the ‘Net. I get MacLife and MacFormat magazines, which both offered help on this topic this month. They covered most of the bases, but I have a few tips they didn’t cover.
So let’s get started, shall we?
How to change the wallpaper to begin with.
You change the desktop, also known as the “wallpaper”, through the Desktop & Screensaver Preference Pane in the System Preferences.
You can access this Preference Pane in three ways:
First, you can go to the Dock and click on the gear icon for System Preferences.
That will open up System Preferences. The top row has the Desktop & Screensaver Preference Pane.

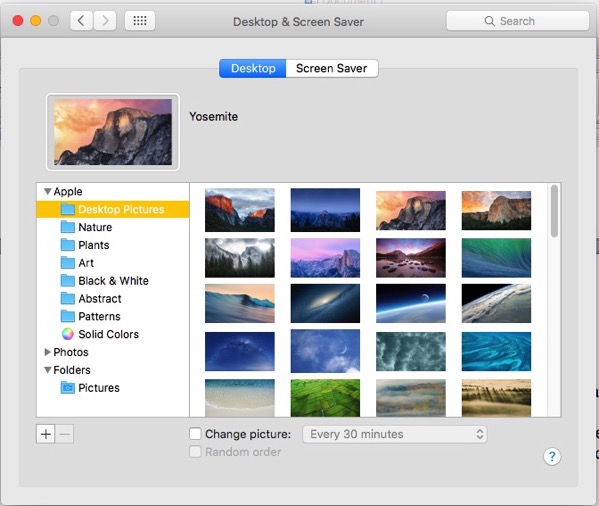
Below it you see a list of folders where Apple provides you with desktops for your use.
Below that, you see Photos, which expands into your Photos pictures.
Below that, you see Pictures, the main folder in your User Account for pictures. Note that it only display the pictures in the folder at the top level and not those enclosed in folders you put into the Pictures folder. I’ll explain how to add a folder in a moment.
To the right of the list of picture locations, you can see the photos in the currently selected folder. Just click on a photo to change the desktop. No rebooting or restarting required.
On the bottom you see two check boxes and a box with a double-headed arrow. The first box lets you change the photos from the current folder at set time intervals. Click on the double-headed arrow to see the choices.
The second check box lets you change pictures randomly.
Now about that Pictures folder in the list of picture locations. You see a “+” and a “-“.
With the plus sign you can add a location and with the minus sign you can delete a location. You don’t delete the pictures themselves, you just tell the Preference Pane not to look in that location any more.
I did say you could access the Desktop Preference Pane in three ways.
The second way to access it is through the Apple Menu at the upper left-hand corner of your Menu Bar. Looks like a stylized Apple with a bite out of it.

Third, you can directly access the Desktop & Screensaver Preference Pane by right-clicking or control-clicking on the desktop itself. You go right to that Preference Pane.

You can use several different file formats as your Mac’s desktop.
You can use PNG files. You can use JPEG files. You can use your old Windows XP desktop wallpaper in .BMP format, too.
If you used Windows or Linux, you can use those desktop files, too.
About the only format you can’t use is the old ZSoft .PCX format. If you have pictures in that format you would like to use, you can use one of several on-line file conversion Web sites.
If you have Windows on another computer or as a virtual machine on your Mac, you can use the free (and awesome) Irfanview to change the format of that old .PCX file.
Some Legal Advice (for what it’s worth)
If you download pictures from a sketchy Web site, you should scan them with a virus checker first. I’m talking about Porn Hub here, not HeidiKlum.com. Just be careful, that’s all.
And if you scanned a photo from an issue of Playboy or Sports Illustrated, Do Not Upload It. These photos are copyrighted and have lots of unphotogenic lawyers on call to sue you. Use it yourself, but don’t share it with your friends. Stupidity of friends is not a defense in court.
With that in mind…
How to Get Pictures from your Web Browser onto Your Desktop with One Click
If you see a picture on the Web that you want to capture for your own use on your own desktop, do the following:
First, using either Safari or Firefox (Chrome won’t do this out of the box), bring up the picture in your Web browser.
Second, right-click on the picture. In Safari, you get the following menu:
Click on the Use Image as Desktop Picture and you’re good to go.
In Firefox, follow the same right-click procedure. You just want to click on the “Set as Desktop Picture” selection.
Where Can I Get Pictures?
For just about any topic, try images.google.com. You will go to Google’s immense database of images. Just type in a search term such as “puppies” and you will get a plethora of puppy pictures. Same for “Kate Upton”
Want “Kate Upton and puppy”? You got it.
If you want astronomy, go to the Astronomy Picture of the Day here. You can choose from NASA’s pictures from space.
You can also try jpl.nasa.gov for the Jet Propulsion Laboratory in beautiful La Canada-Flintridge or the more commercial space.com.
If you want interesting art, go to deviantart.com for work by illustrators. If you like it, send the artist a donation or purchase the artwork for your wall or desk.
How to Exploit Windows Themes (At Least the Pictures) for your Mac desktop
Microsoft has a gallery of Windows themes with prebuilt sound schemes and gorgeous pictures.
These come in files with the .themepack extension. With the right Mac free software, you can expand these files.
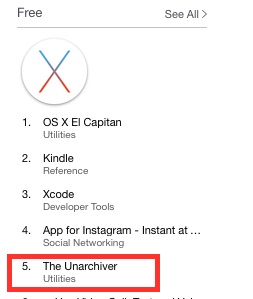
The free software you want is The Unarchiver, available through the App Store.
Go to the top free apps sections at the App Store’s beginning to find it. Just click on it to install it.
With The Unarchiver installed, you can expand a lot of different archive formats. Actually, themepack is not something new that Microsoft dreamed up. It’s just a .zip file relabeled.
So go here to find Microsoft’s own themepack listing. Pick one you like and download it.
Now go to your Download folder and double-click on the themepack file.
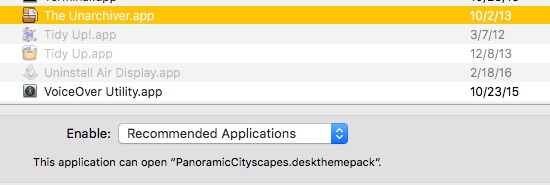
It will come up with this message:
So choose an app! You want the The Unarchiver. It’s either in your /Applications folder or your /Applications/Utilities folder.
Click once on The Unarchiver to highlight it. You should get a message below (it’s in really tiny text) that The Unarchiver is up to the task of expanding this file.
So click on the “Open” button and you should see The Unarchiver briefly pops up in your Dock, quietly doing its thing.
Now go back to your Downloads folder. Above the themepack file you should see a folder with the same name. Open it up and you’ll see….WAV files for the Windows alerts and a folder full of images.
Move the images folder to your Pictures folder, add them to the folders used by the Desktop & Screensaver Preference Pane. You’re all set to go.
And for you at Microsoft, yes, I use and love Windows 10. And I repeat the legal advice I gave above. Use these pictures for your own personal use. Do NOT upload them.
Tom Briant
Editor, MacValley Blog
Senior Correspondent Arnold Woodworth's Weekly Web Wrap-up for February 21, 2016
This software lets you access Windows and Mac OS at the same time
Parallels Desktop 11 is one example of that right software.
http://www.businessinsider.com/parallels-desktop-11-mac-os-windows-virtualization-review-2016-2
Apple Releases Updated Version of iOS 9.2.1 to Fix Devices Bricked by 'Error 53’
The update will restore iPhones and iPads that have been disabled due to "error 53" to full working condition and will ensure that future iOS devices that have had similar repairs will not be fully disabled. Touch ID will not, however, be accessible until Apple-authorized repairs are made to a device affected by the issue.
Apple originally explained that error 53 was intentional, implemented as a way to prevent the use of a malicious Touch ID sensor that could be used to gain access to the Secure Enclave, but customers with bricked devices were not happy with the explanation and Apple found itself facing a class-action lawsuit.
http://www.macrumors.com/2016/02/18/apple-ios-9-2-1-error-53-fix/
Apple re-issues iOS 9.2.1 to fix iPhones bricked by Error 53
Apple re-issued iOS 9.2.1 to fix the "Error 53" that had crippled iPhones whose owners had replaced some parts themselves or had a third-party shop do repairs.
The new iOS 9.2.1 will only be served to users who update their iPhones through iTunes on a Mac or Windows PC. Most iPhone owners retrieve updates over the air using their cellular connection, and so will not receive the replacement.
Even so, the operating system will continue to check for mismatched components, Apple said today. If iOS does detect changed parts, it will still disable Touch ID. The difference: The iPhone as a whole should not be bricked.
http://www.computerworld.com/article/3034863/apple-ios/apple-re-issues-ios-921-to-fix-iphones-bricked-by-error-53.html
Mother uses 'Find my iPhone' to Find her Kidnapped Daughter
http://www.patentlyapple.com/patently-apple/2016/02/mother-uses-find-my-iphone-to-find-her-kidnapped-daughter.html
http://www.techinsider.io/apple-find-my-iphone-app-helped-find-kidnapped-teen-2016-2
How do I transfer music from my old iPad to my new one?
http://www.nytimes.com/2016/02/17/technology/personaltech/moving-music-between-ipads.html?emc=edit_ct_20160218&nl=personaltech&nlid=11893479
27 things you didn't know your iPhone could do
http://www.businessinsider.com/iphone-tips-tricks-and-hidden-features-you-didnt-know-about?op=0#/#respond-to-texts-without-unlocking-your-phone-1
Video:
How to control your iPhone by just talking to it
http://www.techinsider.io/use-iphone-hands-free-hey-siri-2016-2
This article reviews four privacy add-ons for web browsers, but only two of them (Ghostery and Disconnect) work on Mac OS or iOS.
Publishers of the other two say that Mac OS and iOS versions are coming “real soon now”.
http://www.nytimes.com/2016/02/18/technology/personaltech/free-tools-to-keep-those-creepy-online-ads-from-watching-you.html?emc=edit_ct_20160218&nl=personaltech&nlid=11893479
Apple's 'Rigid and Exacting' Recycling Processes Focus on the 'After-Life of an iPhone’
While global brands including HP, Huawei, Amazon and Microsoft also have detailed protocols for recycling their products, Apple’s are the most rigid and exacting.
"There’s an e-waste problem in the world,” said Linda Li, chief strategy officer for Li Tong. "If we really want to leave the world better than we found it, we have to invest in ways to go further than what happens now."
http://www.macrumors.com/2016/02/17/apples-recycling-processes-after-life-of-an-iphone/
http://www.bloomberg.com/news/features/2016-02-16/where-your-iphone-goes-to-die
Entire March issue of Bon Appétit magazine shot exclusively on iPhones
http://9to5mac.com/2016/02/16/bon-appetit-magazine-iphone-issue/
Video:
How Apple makes their Geniuses always seem so happy and helpful
http://www.businessinsider.com/apple-customer-service-secrets-revealed-genius-bar-2016-1
Video:
How to play music from YouTube on your iPhone while using other apps
Clever trick.
http://www.techinsider.io/youtube-music-iphone-display-off-other-apps-2016-2
Video:
This tiny glass chip can store all of human history and last forever
http://www.businessinsider.com/glass-chip-360-terabytes-5d-femtosecond-laser-2016-2
A 19-year-old made a free robot lawyer that has appealed $3 million in parking tickets
Joshua Browder's bot handles questions about parking-ticket appeals in the UK. Since launching in late 2015, it has successfully appealed $3 million worth of tickets.
In the future, people won't likely need to hire lawyers for simple legal appeals — they'll just use a bot.
Bots can't provide full and genuine legal counsel, and it will likely take them several decades to become as sophisticated as humans, says Samuel Woolley, who tracks and studies political bots.
http://www.businessinsider.com/joshua-browder-bot-for-parking-tickets-2016-2
Should the Authorities Be Able to Access Your iPhone?
As a legal matter, the showdown between the Obama administration and Apple touched off Tuesday by the ruling of a federal magistrate judge in California turns on an 18th century law. More practically, though, it boils down to this question: Should you be able to lock your phone so securely that even the F.B.I. cannot open it?
The Obama administration and police officers around the country say no, and their precedent is the past. Homes and cars do not have unbreakable locks. You cannot buy an uncrackable safe. And terrorists and child molesters should not be able to buy a hand-held computer that keeps its secrets forever.
Apple, backed by technologists and civil libertarians, says yes.
http://www.nytimes.com/2016/02/18/us/politics/whether-phones-should-lock-out-the-fbi.html?emc=edit_ct_20160218&nl=personaltech&nlid=11893479&_r=1
Video:
A very good description of the issues surrounding the Justice Department vs. Apple on accessing a terrorist’s iPhone
http://money.cnn.com/2016/02/20/technology/apple-fbi-san-bernardino-shooting/index.html
Tim Cook: Apple won’t comply with court order to ‘hack its own users’
In a strongly worded letter to customers posted on Apple’s AAPL, +1.11% website early Wednesday, Cook called the order an “unprecedented step which threatens the security of our customers” with “implications far beyond the legal case at hand.”
The order, Cook wrote, asks the company “for something we simply do not have, and something we consider too dangerous to create.”
“The government is asking Apple to hack our own users and undermine decades of security advancements which protect our customers — including tens of millions of American citizens — from sophisticated hackers and cybercriminals,” said Cook. “We can find no precedent for an American company being forced to expose its customers to a greater risk of attack.”
http://www.marketwatch.com/story/tim-cook-apple-court-order-threatens-the-security-of-customers-2016-02-17
Donald Trump rips Apple for opposing order to unlock San Bernardino suspect’s phone
Donald Trump wants to know: Who does Apple think it is for refusing to help the Justice Department unlock a phone used by a suspect in the San Bernardino attack?
http://www.marketwatch.com/story/donald-trump-rips-apple-for-opposing-order-to-unlock-san-bernardino-suspects-phone-2016-02-17
Reader comment:
Isn't it quite interesting that even the FBI can't hack Apple ... in a world where hackers are getting into every system imaginable, including the FBI's databases and virtually all of the governments files ... who would you trust with your information?
Mom whose son died in San Bernardino attack sides with Apple
Her son was killed in the San Bernardino, Calif., massacre — but Carol Adams agrees with Apple that personal privacy trumps the feds’ demands for new software to break into iPhones, including the phone of her son’s killer.
The mom of Robert Adams — a 40-year-old environmental health specialist who was shot dead by Syed Rizwan Farook and his wife — told The Post on Thursday that the constitutional right to privacy “is what makes America great to begin with.”
Adams said she understands the FBI’s need to search Farook’s phone, but it has to be done without putting others at risk.
http://www.marketwatch.com/story/mom-whose-son-died-in-san-bernardino-attack-sides-with-apple-2016-02-19
White House says FBI wants access to one iPhone, not blanket backdoor from Apple
Apple Chief Executive Tim Cook himself predicted this argument in his open letter to the public on Wednesday, saying that the government "may argue that its use would be limited to this case." But in Cook's view, "there is no way to guarantee such control."
From Apple's perspective, creating a tool to access a single iPhone could open the flood gates for future issues rippling well beyond the investigation into the San Bernardino shooting.
"In the wrong hands, this software — which does not exist today — would have the potential to unlock any iPhone in someone's physical possession," Cook said.
http://appleinsider.com/articles/16/02/17/white-house-says-fbi-wants-access-to-one-iphone-not-blanket-backdoor-from-apple
Here are three very good editorials about FBI access to Apple iPhones:
http://www.market-ticker.org/akcs-www?post=231125
http://www.market-ticker.org/akcs-www?post=231126
http://www.market-ticker.org/akcs-www?post=231127
JOHN MCAFEE: I'll decrypt the San Bernardino iPhone
John McAfee is running for president as a member of the Libertarian Party.
Using an obscure law, written in 1789 — the All Writs Act — the US government has ordered Apple to place a back door into its iOS software so the FBI can decrypt information on an iPhone used by one of the San Bernardino shooters.
No matter how you slice this pie, if the government succeeds in getting this back door, it will eventually get a back door into all encryption, and our world, as we know it, is over. In spite of the FBI's claim that it would protect the back door, we all know that's impossible. There are bad apples everywhere, and there only needs to be one in the US government. Then a few million dollars, some beautiful women (or men), and a yacht trip to the Caribbean might be all it takes for our enemies to have full access to all our secrets.
The fundamental question is this: Why can't the FBI crack the encryption on its own? It has the full resources of the best the US government can provide.
With all due respect to Tim Cook and Apple, I work with a team of the best hackers on the planet. These hackers attend Defcon in Las Vegas, and they are legends in their local hacking groups, such as HackMiami. They are all prodigies, with talents that defy normal human comprehension. About 75% are social engineers. The remainder are hardcore coders. I would eat my shoe on the Neil Cavuto show if we could not break the encryption on the San Bernardino phone.
And why do the best hackers on the planet not work for the FBI? Because the FBI will not hire anyone with a 24-inch purple mohawk, 10-gauge ear piercings, and a tattooed face who demands to smoke weed while working and won't work for less than a half-million dollars a year. But you bet your ass that the Chinese and Russians are hiring similar people with similar demands and have been for many years.
Interesting reader comments to this story.
http://www.techinsider.io/john-mcafee-ill-decrypt-the-san-bernardino-iphone-for-free-so-apple-doesnt-need-to-place-a-back-door-on-its-product-2016-2
http://www.techinsider.io/john-mcafee-iphone-backdoor-terrible-idea-2016-2
Security firm shows how Apple could bypass iPhone security to comply with FBI request — or so it claims
All this supposes that iPhone is only protected by a 4-digit passcode, however. If a complex password was used, no-one in the FBI would live long enough to gain access.
http://9to5mac.com/2016/02/17/apple-fbi-court-order-method/
Apple has positioned itself as a model global citizen whose devices command a premium because of the lengths it goes to safeguard customers' personal data.
"Apple is legitimately concerned about its ability to retain the trust of users globally,” David Kirkpatrick said. "The last thing (Apple CEO) Tim Cook wants to do is shoot himself in the foot by making customers in Peru, China, India, Indonesia, Nigeria and Saudi Arabia think that his company would cooperate with their governments in infringing on their privacy.”
http://www.usatoday.com/story/tech/news/2016/02/18/global-profits-stake-apple-tech-fight-us-security/80552114/
Legendary iPhone hacker weighs in on Apple’s war with the FBI
http://bgr.com/2016/02/18/apple-fbi-backdoor-will-strafach-opinion/
Mozilla chief: FBI snooping at Apple 'back door' makes you less safe
Encryption is what keeps communications between parties safe from prying eyes. Encryption shields sensitive data, like medical records and banking information. It makes it possible to send confidential documents. And it enables greater good: human rights workers, journalists and whistle-blowers can defend what's right without placing themselves in danger. Most of us use encryption every day without even knowing it.
But it is under threat: In the United States, federal agencies like the FBI are calling on tech companies to facilitate access to encrypted communications.
http://www.cnn.com/2016/02/18/opinions/apple-encryption-backdoor-fbi-surman/
Apple Unlocked iPhones for the Feds 70 Times Before
Apple’s stance in the San Bernardino case may not be quite the principled defense that Cook claims it is. In fact, it may have as much to do with public relations as it does with warding off what Cook called “an unprecedented step which threatens the security of our customers.”
Apple acknowledged that the phone in the meth case was running version 7 of the iPhone operating system, which means the company can access it. “For these devices, Apple has the technical ability to extract certain categories of unencrypted data from a passcode locked iOS device,” the company said in a court brief.
Apple’s argument in New York struck one former NSA lawyer as a telling admission: that its business reputation is now an essential factor in deciding whether to hand over customer information.
http://www.thedailybeast.com/articles/2016/02/17/apple-unlocked-iphones-for-the-feds-70-times-before.html
The San Bernardino County government said the FBI told its staff to tamper with the Apple account of Syed Farook (who with his wife, Tashfeen Malik, carried out the December shooting in which 14 people were killed).
The development matters because the change made to the account – a reset of Farook’s iCloud password – made it impossible to see if there was another way to get access to data on the shooter’s iPhone without taking Apple to court.
“The county was working cooperatively with the FBI when it reset the iCloud password at the FBI’s request,” read a post on San Bernardino County’s official Twitter account.
Apple, which has the technical ability to get inside an iCloud account but not always an individual phone, has already provided the FBI with any iCloud data it has for Farook. Those backups only go back to 19 October, six weeks before the shooting.
That feature is disabled as a security precaution if someone changes the iCloud password for an account.
According to Apple, this also made the information on the iPhone permanently inaccessible.
http://www.theguardian.com/technology/2016/feb/20/san-bernadino-county-fbi-gunman-apple-account
North Carolina Senator Richard Burr, chairman of the Senate Intelligence Committee, is working on legislation that would penalize companies that don't comply with court orders to unlock encrypted devices
http://www.macrumors.com/2016/02/18/senator-punish-bill-dont-encrypt/
Apple has refused, arguing that to do so would set a legal precedent that could force it to hack a suspect’s phone each time authorities face a warrant. It argues that would violate user trust, privacy norms and weaken the core security of the company’s flagship smartphone.
Early Friday, the Justice Department released a lengthy legal filing that accused Apple of misinterpreting the law and placing marketing goals over national security.
The FBI conceded this week it can’t force Apple to give it the passcode, but it concocted a clever workaround. It persuaded a judge to order Apple to make it easier to guess the passcode by weakening other countermeasures.
http://www.theguardian.com/technology/2016/feb/19/apple-fbi-encryption-battle-san-bernardino-shooting-syed-farook-iphone
N.S.A. Gets Less Web Data Than Believed, Report Suggests
The report indicates that when the N.S.A. conducts Internet surveillance under the FISA Amendments Act, companies that operate the Internet are probably turning over just emails to, from or about the N.S.A.’s foreign targets — not all the data crossing their switches, as the critics had presumed.
The theory that the government is rooting through vast amounts of data for its targets’ messages has been at the heart of several lawsuits challenging such surveillance as violating the Fourth Amendment.
http://www.nytimes.com/2016/02/17/us/report-says-networks-give-nsa-less-data-than-long-suspected.html
How to Create a More Secure Passcode on Your iPhone or iPad
Apple doesn't advertise it, but the iOS operating system offers an option to make your passcode even more secure through the use of an alphanumeric passcodes or custom length numeric passcodes. Alphanumeric passcodes contain letters and numbers. Both alphanumeric and custom numeric passcodes can be much longer than four or six digits.
http://www.macrumors.com/how-to/create-a-more-secure-passcode-on-ios-devices/
Apple’s $450 million e-book settlement Is affirmed by court
A federal appeals court Wednesday affirmed a $450 million e-books settlement between Apple Inc. and a group of plaintiffs, the latest development in long-running antitrust allegations against the company.
http://www.marketwatch.com/story/apples-450-million-e-book-settlement-is-affirmed-by-court-2016-02-17
There's finally an explanation for the giant dirt pyramid on Apple's new campus
It will become part of the building's landscaping, which will eventually resemble a natural forest.
http://www.businessinsider.com/we-now-know-why-theres-a-giant-dirt-pyramid-on-apples-new-campus-2016-2
History: Some Stories of “Perfect” Security
Nathan Cooprider is senior software engineer at Threat Stack, and Sam Bisbee is CTO, and they brought up the Tor as a great example of a technology long believed to be impregnable that's now been compromised in various ways, all of which reveal the ways a single vulnerability can negate many layers of strength.
The danger with mathematically perfect encryption or theoretically invulnerable software is that the user tends to extrapolate to the entire system and gain a false sense of security. As Bisbee put it, "detection is the new prevention." If the goal previously was to build an unhackable system, the new goal is a system that can tell us when it's been breached, and tell us quickly. No system can be 100% safe, but a system protected by a defense-in-depth philosophy can recover more quickly in the real world of real threats.
http://www.csoonline.com/article/3033426/security/unbreakable-security-that-wasnt-true-tales-of-tech-hubris.html
Your New Television is Spying on You
"Please be aware that if your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party through your use of Voice Recognition," Samsung posted in its SmartTV privacy policy.
http://www.market-ticker.org/akcs-www?post=231122
http://money.cnn.com/2015/02/09/technology/security/samsung-smart-tv-privacy/index.html
Hollywood hospital pays hackers $17,000 ransom to restore computers
http://www.marketwatch.com/story/hollywood-hospital-pays-hackers-17000-ransom-to-restore-computers-2016-02-18
Fighting Fraud on Multiple Fronts
Q. Do credit card companies send customers text messages about their accounts, or is this yet another hacking scheme?
A. If you have not specifically signed up for text alerts, any messages sent to your phone concerning “deactivated,” “blocked” or “locked” accounts and asking you to call a supplied telephone number are most certainly frauds. (Poor spelling and messages claiming to be from banks you do not use are further indicators of fraudulent intentions.) Do not call the number or attempt to block future messages by replying “STOP” — which just confirms you got the message. As the Federal Communications Commission advises, most wireless providers allow you to forward the unwanted message to 7726 (SPAM) to block the sender.
http://www.nytimes.com/2016/02/18/technology/personaltech/fighting-fraud-on-multiple-fronts.html?emc=edit_ct_20160218&nl=personaltech&nlid=11893479
Blog Archive
-
▼
2016
(123)
-
▼
February
(7)
- I Review the Dell P2416D 24" monitor
- Senior Correspondent Arnold Woodworth's Weekly Web...
- Beginner's Column-How to change the desktop pictur...
- Senior Correspondent Arnold Woodworth's Weekly Web...
- Senior Correspondent Arnold Woodworth's Weekly Web...
- Senior Correspondent Arnold Woodworth's Weekly Web...
- Find the Home and End buttons on a Mac - How to - ...
-
▼
February
(7)