The MacValley blog
![]()
Welcome to the MacValley blog, your first stop for all the latest MacValley news and views.
|
The MacValley blog Editor: Tom Briant
|
Labels used in posts
|
To search the blog posts please use the box below
Thursday, May 29, 2014
Monday, May 26, 2014
Steve Ballmer interested in buying NBA's Clippers? - CNET
This is only peripherally related to Macs. But the idea of Steve Ballmer buying the Clippers just tickles me.
Steve Ballmer interested in buying NBA's Clippers? - CNET: ""
(Via.)
How To Completely Customize Your Mac | Mac|Life
People, you’ve wanted to change your Mac’s appearance ever since you bought your Mac. While it’s not as customizable as the Classic OS, you can do a lot to make your Mac uniquely yours. So go to the link to the great Maclife article on this topic.
Now the article mentions the Visage program. I don’t know if it still works with 10.9. I can tell you that OS X 10.9.3 works with Flavourshttp://flavours.interacto.net
Tom Briant
Editor, MacValley Blog
How To Completely Customize Your Mac | Mac|Life: ""
(Via.)
Rumor: Apple working on ARM-based Mac variants with larger trackpad built into keyboard | 9to5Mac & AppleInsider
Here’s today’s winner for most fun rumor. Is Apple working on new Macs using the same kinds of chips (ARM) used in its iOS devices? With the trackpad built into the keyboard?
Read the comments.
I am sure that Apple has built prototypes of Macs running all sorts of CPUs. We know that Apple ran a parallel effort to put OS X on Intel chips from the very start of OS X development. So I’m sure that OS X has been compiled to run on a wide range of processors, albeit with varying degrees of success and/or practicality.
Tom Briant
Editor, MacValley Blog
Rumor: Apple working on ARM-based Mac variants with larger trackpad built into keyboard | 9to5Mac: ""
(Via.)
Slipping shipping times may support analyst prediction of new, cheaper iMacs launching at WWDC | 9to5Mac
An analyst predicts that Apple will introduce new iMacs at WWDC.
Tom Briant
Editor, MacValley Blog
(Via.)
Mac OS X software update temporarily broken, likely due to expired SSL certificate | 9to5Mac
Someone at Apple forgot to renew the SSL certificate for Software Update. Guess Apple is ultimately, all too human.
Tom Briant
Editor, MacValley Blog
Mac OS X software update temporarily broken, likely due to expired SSL certificate | 9to5Mac: ""
(Via.)
Sunday, May 25, 2014
It's Weekend Wrapup time from Senior Correspondent Arnold Woodworth
Steve Jobs Sent This Inspiring Email To A Startup Who Helped Design One Of The First iPad Apps
http://www.businessinsider.com/steve-jobs-email-to-y-media-labs-2014-5
Apple's Mac Pro ship times fall below one week for first time since launch
http://appleinsider.com/articles/14/05/24/apples-mac-pro-ship-times-fall-below-one-week-for-first-time-since-launch
iMessage Flaw Bugs Apple
Apple vowed Tuesday to fix a persistent bug in its iOS mobile operating system that punishes former iPhone users. The flaw, which has been in iMessage since the release of iOS 5, prevents former iPhone users from receiving SMS messages from current users.
http://www.technewsworld.com/story/80499.html
Apple too late to stop massive iCloud breach, hackers claim
http://www.cultofmac.com/280189/icloud-hacker-calls-apples-response-little-late/
Boeing CEO wants to emulate Apple strategy
Mr. McNerney said Boeing is shying away from trying to make big technological leaps every 25 years, focusing on the less-risky approach of incremental improvements when it plans new jets.
AW comment: Steve Jobs success was mainly due to two big tech leaps: The iPod (music player) and the iPhone. An incremental approach would NEVER have brought those into existence.
http://www.marketwatch.com/story/boeing-ceo-wants-to-emulate-apple-strategy-2014-05-21
Boeing Might Be Copying Apple's Innovation Policies But It Doesn't Understand Them
http://www.forbes.com/sites/timworstall/2014/05/22/boeing-might-be-copying-apples-innovation-policies-but-it-doesnt-understand-them/
The Schools Where Apple, Google, and Facebook Get Their Recruits
http://www.wired.com/2014/05/alumni-network-2/
The 15 Highest-Grossing iPhone And iPad Games
http://www.businessinsider.com/highest-grossing-iphone-and-ipad-games-2014-5
Fully 40% of human resources executives say they don't check social media before hiring employees and another 38% say they only sometimes do. And perhaps more importantly, of the hiring managers that did check social media, only 6% said that it had a significant impact on their hiring decision.
There is no way of telling how a prospective employer treats or reacts to social media impressions ... as with most endeavors, it is probably best to err on the side of caution and consider your social media activity as an open book that will be factored into hiring decisions.
http://www.marketwatch.com/story/bosses-dont-care-about-your-facebook-twitter-profiles-2014-05-19
How to Use #Hashtags on Twitter and Facebook
hashtags are a simple way to group conversations ........ to organize content into a large conversation
hashtags should be used around a very specific conversation bounded by both topic and time
users are driven by three motivations: Self-expression, human connection and content discovery
http://www.cio.com/article/753155/How_to_Use_Hashtags_on_Twitter_and_Facebook
Too much sharing and 'liking' on social network could reveal emotional stress
a new study finds that oversharing on Facebook is also a sign of loneliness.
http://www.marketwatch.com/story/lonely-people-post-personal-details-on-facebook-2014-05-21
Facebook Gets Nosier Than Ever
Facebook recently made it even simpler to pry into your friends' private affairs on the social network.
Specifically, the Ask button -- which already has been available to those seeking more information about many other aspects of a given user's life -- now is an option when it comes to a user's relationship status as well.
It's definitely effective for Facebook, which gets to gather more user data.
http://www.technewsworld.com/story/80484.html
The NSA Doesn't Need To Hack Your Phone
Facebook does it for them.
Facebook’s mobile app just grew a keen sense of hearing. Starting Wednesday, the app has the ability to recognize music and television shows playing in the vicinity of users.
The feature is designed to make it easier for users to share. When users begin to write a post, the Facebook app will offer to include information about music or shows playing in the background.
And maybe listen to your conversations with friends.
Wiretapping laws are not an issue, right? Facebook says so.
http://www.market-ticker.org/akcs-www?post=229032
The death of privacy over your medical records
the US Government has effectively mandated electronic medical records
The federal government is piecing together a sweeping national “biosurveillance” system that will give bureaucrats near real-time access to Americans’ private medical information in the name of national security.
http://www.market-ticker.org/akcs-www?post=229029
How bickering and greed neutered the 'Do Not Track' (DNT) privacy initiative
Yes, if you turn it on in your browser, it sends a signal in the form of an HTTP header to Web companies' servers. But it probably won't change what data they collect.
That's because most websites either don't honor DNT
http://www.pcworld.com/article/2158220/do-not-track-oh-what-the-heck-go-ahead.html
Antonin Scalia Totally Gets Net Neutrality
In 2005, the justice told us to imagine the Internet was a pizzeria. We should've taken his advice.
If there's an original sin in this [net neutrality] story-the moment that set in effect the entire fight over net neutrality-it happened in 2002.
The problem that the FCC is now facing-the reason it's talking about "commercial reasonableness"-is all a result of that 2002 regulatory decision to treat broadband Internet like an information product, rather than as electronic infrastructure.
http://www.theatlantic.com/technology/archive/2014/05/net-neutralitys-little-known-hero-antonin-scalia/361315/
Obama, alas, lets us down on net neutrality
Opinion: His FCC chairman is quietly letting the industry rewrite the rules
Obama appointed the current FCC commissioner, Tom Wheeler, a former lobbyist for the telecommunications industry
professional FCC watchers report that various passages from the proposal confirm a shift toward a looser definition of net neutrality that allows for paid prioritization of content
Wheeler is really an industry tool that has been put in place at the FCC to reward campaign donors and further the interests of the very industry he is charged with regulating while taking pains to craft a public perception that the administration remains true to Obama's campaign pledges to uphold net neutrality.
http://www.marketwatch.com/story/obama-alas-lets-us-down-on-net-neutrality-2014-05-21
How to Fight the Battle for Net Neutrality
http://gizmodo.com/how-to-fight-the-battle-for-net-neutrality-1577488538
Hackers Paint Bull's-eyes on Cyber-currencies
http://www.technewsworld.com/story/80475.html
Con men used credit-card fraud to rob banks of $200 million.
The real scandal is how easy it was
So how did they do it? Apparently it was a simple three-step process.
The first was to create a fake identity.
They would make up a fake person and add him or her as an authorized user on their card.
And once that fictitious user existed, they just started apply for lots more credit cards in that person's name.
The second step was to pump up that user's credit score.
They set up sham companies, and then just applied to the credit card companies for card terminals.
the card companies deposited the money in these sham companies' bank accounts.
http://www.marketwatch.com/story/how-to-steal-200-million-2014-05-19
Saturday, May 24, 2014
Use the Finder's tags feature from the keyboard | Macworld
Like the Tags feature in Mavericks, but wish you could tag files from the keyboard?
Dan Frakes of Macworld shows you how.
Use the Finder's tags feature from the keyboard | Macworld: ""
(Via.)
Wednesday, May 21, 2014
The Big List of 111+ Keyboard Shortcuts For The Most-Used Online Tools
This comes from Bufferapp.com via Lifehacker.com. Thanks, Melanie Pinola, for sharing this with us.
The Big List of 111+ Keyboard Shortcuts For The Most-Used Online Tools: ""
(Via.)
Tom Briant
Editor, Macvalley Blog
Useful and fun Web site for your chronologic needs
You’ll often need a timer while using your Mac. You can download many dedicated timer apps; but you may not want to dump another one-trick pony into your Applications folder.
Then let me recommend a Web site that can help you with your timer needs. The Web site is onlineclock.net
You start out with a digital clock with an alarm feature. You set the clock to the time you want it to ring. And it makes a loud, obnoxious ring when it’s time! You can’t ignore it! You’ll have to interrupt your game or whatever to turn it off, then take the clothes out of the washer.
In the upper left-hand corner, you can choose four different sizes of digital display. They range from small to EXTRA-LARGE. Even with my myopic eyes, I can make out the extra-large digits.
In the upper right-hand corner, you can set the background color as either blue, black (the default), silver, green or orange.
But That’s Not All!
OnlineClock.net comes with a dedicated timer at timer.onlineclock.net
Fun features!
Want an aquarium with your clock? Just pick the aquarium setting and you can choose between four different aquariums.
Want to see and hear rain on your screen? Or a crackling fireplace? Handy for those of us in studio condos.
Onlineclock.net hooks into videos from YouTube to display these moving backgrounds.
You can have a lot of fun with onlineclock.net, as well as just count down to when your towels can come out of the dryer.
Tom Briant
Editor, MacValley Blog
Monday, May 19, 2014
Mac keyboard shortcuts - Matt Gemmell
Great Article on Mac Keyboard Shortcuts
Tom Briant
Editor, MacValley Blog
Mac keyboard shortcuts - Matt Gemmell: ""
(Via.)
Saturday, May 17, 2014
It's time for Senior Correspondent Arnold Woodworth's weekly roundup
OS X 10.9.3, iTunes 11.2 arrive with bug fixes, feature enhancements
http://www.macworld.com/article/2155289/os-x-10-9-3-itunes-11-2-arrive-with-bug-fixes-feature-enhancements.html
Apple Inc. and Google Inc. agreed to dismiss all lawsuits between them, bringing to a close a patent dispute between the iPhone maker and the Web giant's Motorola unit.
http://www.marketwatch.com/story/apple-and-google-agree-to-dismiss-all-lawsuits-2014-05-16
Apple's Beats buy is just stupid
http://blogs.marketwatch.com/cody/2014/05/12/apples-beats-buy-is-just-stupid/
A "little" Chinese company just rolled out a new tablet aimed at challenging Apple Inc. - at least in China.
http://blogs.marketwatch.com/thetell/2014/05/15/apple-ipad-faces-new-challenger-in-little-xiaomis-mi-pad/
Steve Jobs' run of introducing disruptive products has been really amazing.
Expecting Apple to keep coming up with disruptive products that are game changing hits is not realistic.
http://techpinions.com/the-reinvention-of-apple/30525
Wearable technology can predict and prevent disease
Today, wearable technology, coupled with mobile apps, allow people to track a wide variety of vital signs and health functions.
With greater access to our own body's data, we can take a larger step towards ensuring and lengthening our own survival.
http://www.marketwatch.com/story/what-you-wear-will-be-a-life-or-death-matter-2014-05-15
Why I Just Can't Quit Facebook
I rely on Facebook to help maintain friendships more than I want to admit.
The problem was that Facebook knows more about me than many of those friends do.
Facebook knows what movies I like, where I live, who my best friends are, and what apps I use, because I have spent the last seven years giving it that information. Now that I’ve decided I prize my privacy more than my posts, it’s too late to back out.
Facebook is no longer just a place for friends, but a pervasive and invasive identity manager. The social network wants to be privy to what we do online, and control who gets that information. Facebook may be where my friends hang out, but it isn’t my friend.
It’s hard to take Facebook's complaints about government surveillance seriously when it’s a far more efficient spy on our lives.
Leaving Facebook made me realize who my real friends are. So now, rather than quitting Facebook, I'm going to cull my friends list from 418 to around 100 or so.
By eliminating the noise and deleting some personal information, such as Likes and my location, I can go back to using Facebook for what it began as—a place for friends.
Until there’s another service that all the people I care about use, I’m stuck under Facebook’s big, blue thumb. I can't click Like on this situation.
http://www.businessinsider.com/why-i-just-cant-quit-facebook-2014-5
How Young Is Too Young for a Digital Presence?
Some parents savvy in matters of social media are establishing web and email accounts, not to mention usernames, for their newborns.
But there could be a risk here.
http://www.nytimes.com/2014/05/15/technology/personaltech/how-young-is-too-young-for-a-digital-presence.html?_r=0
You will never, ever be 'forgotten' on the Internet
Anybody would want embarrassing information about themselves - photos, videos, comments, documents, etc. - erased from the Internet. But how difficult is that? The answer may scare you.
You simply can't completely and irrevocably erase your digital existence from the World Wide Web because it's almost impossible to guarantee the complete removal of even one file.
Having your files published on Web sites isn't your biggest concern. Knowing your file ended up permanently on the hard drives of thousands of strangers who could republish it at any given moment is.
http://www.marketwatch.com/story/you-will-never-ever-be-forgotten-on-the-internet-2014-05-15
The Internet has much to say about the recent ruling by the Court of Justice of the European Union, which determines that if a person wants some personal information removed from Google's search engine, that person has the right to appeal to Google (GOOG) for redress.
I, too, believe that as much information as possible should be available, and that the Web is a uniquely wonderful mechanism for achieving that. But, in this case, I believe the EU did the right thing, and the United States should learn from the court's decision.
In the 1990s one person had submitted a funny letter about sex to a contest. Our magazine had republished that letter. Later, in 2007, that article was the first search result to show up in a search for the person's name. He was out of work and in the middle of a job hunt. By the tone of the e-mail, he was panicking. What would a prospective employer make of this joking sex letter?
things that are public often become private in time, largely because keeping them persistently public has been impossible. Until a decade ago, the past was the domain of historians. Now we live in a history glut.
http://www.businessweek.com/articles/2014-05-16/ungoogle-me-the-case-for-scrubbing-search-results
Hundreds of convicted criminals have demanded that their past misdemeanours are expunged from Google searches after a contentious European court decision.
http://www.thetimes.co.uk/tto/technology/internet/article4092639.ece?CMP=OTH-gnws-standard-2014_05_16
5 Arguments Against Net Neutrality
http://mashable.com/2014/05/16/5-arguments-against-net-neutrality/
The Supreme Court Is Clueless When It Comes To Tech
http://www.businessinsider.com/r-in-us-when-high-tech-meets-high-court-high-jinks-ensue-2014-09
First Amazon patented "One Click". Now This:
A photography site called DIY Photography wrote this week that the Amazon corporation applied for—and received—a patent for the process of taking a picture of an object against a white background.
Despite the technical detail in the patent documentation, the DIY site says, Amazon is ultimately claiming exclusive rights to a basic version of an extremely common practice
http://www.businessinsider.com/white-background-amazon-2014-5
How to Score a Job at a Completely Virtual Company
http://mashable.com/2014/05/12/virtual-workplaces-hiring/
How to identify and protect yourself from scams
http://www.marketwatch.com/story/how-to-identify-and-protect-yourself-from-scams-2014-05-16
Monday, May 12, 2014
Some Comedy about the Beats Electronics and Apple deal
Susie Ochs at Macworld posted this picture of a black and white cat listening to music through the owner’s Beats headphones. I presume it’s rap it’s listening to.
Meanwhile, off to the right, Monoprice jumps at the opportunity to offer you headphones of comparable quality at a much, much better price.
As of 10:09 PM, Appleinsider speculates that Apple may wait until WWDC in June to formally introduce Jimmy Iovine and Andre “Dr. Dre” Young as new Apple executives.
The Monoprice headphones are really good. I use them.
Tom Briant
Editor, MacValley Blog
Sunday, May 11, 2014
Senior Correspondent Arnold Woodworth has a Mother's Day roundup of articles for you
Your iPhone Gathers A Lot More Of Your Location Data Than You Thought — Here's How To Disable It
It's a setting called "Frequent Locations"; as you go about your daily routine, your iPhone makes note of where you are and how long you're there. When it starts detecting patterns, it marks the spot as one such "frequent location."
The word from Apple is that "this data is kept solely on your device and won't be sent to Apple without your consent.
http://www.businessinsider.com/iphone-frequent-locations-2014-4#!IDLch
A few weeks ago, I noticed that email attachments within the iOS 7 MobileMail.app are not protected by Apple's data protection mechanisms. Clearly, this is contrary to Apple's claims.
http://www.andreas-kurtz.de/2014/04/what-apple-missed-to-fix-in-ios-711.html
People Are Tracking Thieves Using "Find My IPhone" And Then Hunting Them Down With Hammers
Think about that for a second. People are willing to go all Oldboy on strangers--who may or may not have actually taken the thing--for an Apple gadget.
The report speaks to anti-theft legislation calling for a "kill switch," which would effectively render the expensive gadgets useless bricks remotely by wiping them clean and making them unusable. While phone-makers like Samsung and police departments across the country have been calling for such a feature for years--arguing that a kill switch would effectively nullify the secondary economy thieves need to resell goods--carriers like AT&T, Verizon, and others have been vehement in their opposition.
Why? They claim they would lose money. Most recently, an anti-theft bill proposed in California was killed in the state senate.
http://www.fastcompany.com/3030081/fast-feed/people-are-tracking-thieves-using-find-my-iphone-and-then-hunting-them-down-with-h?partner
Berkeley Apple Store glass entrance is latest to be smashed by car
http://appleinsider.com/articles/14/05/09/berkeley-apple-store-glass-entrance-is-latest-to-be-smashed-by-car
Apple MacBook Air 13-Inch
Rated Excellent
http://www.pcmag.com/article2/0,2817,2457827,00.asp
Why The Beats Deal Makes Perfect Sense For Apple
http://www.forbes.com/sites/ericjackson/2014/05/09/why-the-beats-deal-makes-perfect-sense-for-apple/
The Reason for Apple’s Massive $3 Billion Beats Deal? Spotify
http://time.com/93557/apple-beats/
With Beats, Apple Could Buy The Future Of Music Instead Of Inventing It Again
In digital music, Apple needs only to maintain its lead into the next paradigm shift, and it’s already been working on that.
http://readwrite.com/2014/05/09/beats-apple-buys-the-future#awesm=~oDVkpynshmnCdv
Not even Dr. Dre can make Apple cool again: The iPhone maker needs to create its own buzzworthy products
http://www.marketwatch.com/story/apple-cant-get-its-groove-back-by-buying-beats-2014-05-09
Apple is showing another symptom of a mid-life crisis.
Apple's interest in headphone maker Beats Electronics suggests it feels the need to open its wallet in order to keep up with the cool kids.
Once Apple goes down the road of buying things it doesn’t think it can build, it’s hard to know where it will stop.
http://dealbook.nytimes.com/2014/05/09/apples-mid-life-crisis/
Here's a detractor on the Beats deal:
On the surface, the Beats doesn’t make any sense to me.
Nothing from Beats looks like Apple. Not the brand, not the hardware.
http://daringfireball.net/linked/2014/05/08/beats
http://www.businessinsider.com/beats-acquisition-against-apples-soul-2014-5
Apple ends opposition to smartphone 'kill switch'
Kill switches are aimed at curbing muggings as thieves go after victims' phones.
http://www.bizjournals.com/sanjose/news/2014/05/07/apple-ends-opposition-to-smartphone-kill-switch.html
Family unity doesn't extend to Apple IDs
As parents come to realize the limitations of their Apple ID and Google Play strategies, they are frustrated. All the apps, songs and movies they've purchased are quarantined in their own accounts. When the kids branch out to their own devices, they pretty much just have to start over, with limited workarounds.
http://www.reuters.com/article/2014/05/07/us-smartphone-id-limits-apple-idUSBREA460KR20140507
Apple Crushes Samsung In Korean Customer Satisfaction Survey
http://www.businessinsider.com/apple-samsung-survey-2014-5
Apple's Mac Pro ship times drop to 2-3 weeks, shortest wait since launch
http://appleinsider.com/articles/14/05/08/apples-mac-pro-ship-times-drop-to-2-3-weeks-shortest-wait-since-launch
Apple has publicly released a set of guidelines for law enforcement agencies to request data relating to the company's users.
The guidelines, which were published on Apple's web site, say the company will notify customers when their information is being sought as part of a legal process, except in cases where providing notice would be illegal or put people in danger.
Rainey Reitman, activism director for the Electronic Frontier Foundation, called Apple’s statement “a big step forward.”
http://bits.blogs.nytimes.com/2014/05/08/apple-publishes-expanded-report-on-how-it-handles-government-data-requests/?_php=true&_type=blogs&_r=0
http://www.marketwatch.com/story/apple-to-authorities-show-warrant-to-get-data-2014-05-09
http://www.zdnet.com/apple-reveals-us-government-data-request-guidelines-7000029223/
In a new document for US law enforcement agencies, Apple has explained, in some detail, what can be recovered from locked iOS devices.
http://www.techrepublic.com/article/apple-details-what-can-be-recovered-from-locked-iphones/
Steve Ballmer's math on Apple innovation doesn't add up
Some good history on Apple innovations.
http://www.zdnet.com/steve-ballmers-math-on-apple-innovation-doesnt-add-up-7000029055/
Apple Dominates Worldwide Computer Market Despite iPad Drop
http://wallstcheatsheet.com/technology/apple-dominates-worldwide-computer-market-despite-ipad-drop.html/?a=viewall
http://9to5mac.com/2014/05/09/despite-decline-in-ipad-sales-apple-remains-1-in-combined-pc-tablet-sales/
Apple Jumps to Second Place in Online Retail
http://blogs.wsj.com/corporate-intelligence/2014/05/06/apple-jumps-in-rankings-now-second-largest-online-seller/
Researchers Have Created An iPhone App That's Better At Detecting Skin Cancer Than Your Doctor
Early testing has found the device to be accurate 85% of the time, which is similar to the accuracy rate for dermatologists.
http://www.businessinsider.com/iphone-app-for-detecting-skin-cancer-2014-5
How Steve Wozniak Wrote BASIC for the Original Apple From Scratch
http://gizmodo.com/how-steve-wozniak-wrote-basic-for-the-original-apple-fr-1570573636
5 easy ways to make a hacker's life harder
1. When buying online, use a prepaid debit card.
4. When posting on social networks (or anywhere else, for that matter), consider this rule: If you wouldn't say it publicly, don't say it at all. This goes especially for Facebook, which never deletes data it has on its users . So don't tell everyone you're going on vacation - in doing so, you may be informing burglars that your home is vacant.
5. Break the habit of creating relevant passwords (that is, dates of important events in your life, your loved ones, etc.). Such data can easily be found online and used in hacker attacks. Use password generators.
http://www.marketwatch.com/story/5-easy-ways-to-make-a-hackers-life-harder-2014-05-06
A very good video on social media.
Smart phones and dumb people.
http://www.market-ticker.org/akcs-www?post=228985
Audio:
News websites unleash the comment police
http://www.marketwatch.com/story/news-websites-unleash-the-comment-police-2014-05-08
FTC says Snapchat misled users on disappearing messages
the FTC said "attackers" were able to "compile a database of 4.6 million Snapchat user and phone numbers" because Snapchat did not secure its Find Friends feature.
http://www.marketwatch.com/story/snapchat-misled-users-on-disappearing-messages-says-ftc-2014-05-08-14912021
5 Ways Snapchat Violated Your Privacy, Security
http://www.informationweek.com/software/social/5-ways-snapchat-violated-your-privacy-security/d/d-id/1251175
Snapchat Makes FTC Privacy Charges Disappear
Snapchat has agreed to a settlement with the United States Federal Trade Commission to resolve privacy issues resulting from a hacker's publication in January of data associated with 4.6 million of its users.
http://www.technewsworld.com/story/80430.html
The SEC on Bitcoin: Here there be monsters: Regulators know they can barely protect Bitcoin buyers
http://www.marketwatch.com/story/the-sec-on-bitcoin-here-there-be-monsters-2014-05-09
The Peril of Knowledge Everywhere
Big Brother couldn’t have imagined we’d tell him where we were, who we talk to, how we feel – and we’d pay to do it.
People call for regulation, but regulation is slow-moving, and the analysis will just go somewhere else.
one bit here and another there, both innocuous, may reveal something personal that is hidden perhaps even from myself.
http://bits.blogs.nytimes.com/2014/05/10/the-peril-of-knowledge-everywhere/
Saturday, May 10, 2014
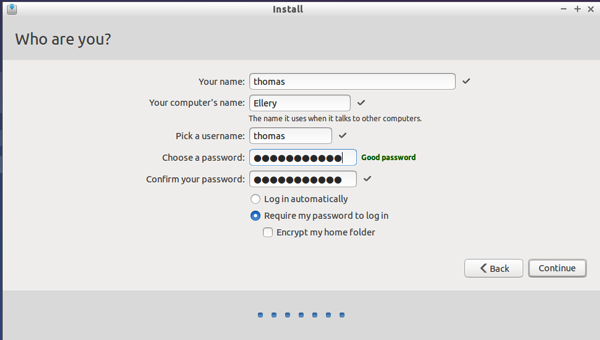
The OS X Friendly Linux Music Server-I try it again
Posting a preview of a MacValley Voice article about the forked-daapd Linux music software and how to install it from the Debian Linux repositories into Ubuntu Linux has proven my most popular article. When I Google myself on this topic, I see that my old post pops to the top of the listings.
I feel some embarrassment about this. forked-daapd has not kept up with the times. It stops playing a streamed track from a Linux iTunes music server after a few minutes. I can only apologize to those of you who read my article in hopes of solving the iTunes music server conundrum, only to find yourselves thwarted. My apologies.
So I’ve looked for a solution to this problem. I’ve looked for an update to forked-daapd past the 0.19 model in the Ubuntu Linux repository from other writers. They may well have solved the puzzle, but I haven’t found it in an easily installable format that I could recommend.
But now, I have found an answer that I found easy to install and doesn’t stall after a few minutes. That answer is called Tangerine. It’s in the Ubuntu Linux software repositories.
Building on two previous articles, one by Arvind Srinivasan in Mac|LIfe online and another by Isa Raffee on their WordPress blog; I built a music serving system that works with the latest version of iTunes. Now, it may not work with future versions of iTunes, so be forewarned. But enjoy it for now.
To begin with, you need a PC. Maybe it’s one that you used to run Windows XP or Windows Vista or 7. In any event, it’s just serving as an end table in your workspace.
So first off, you need to install Linux. I used the light-weight Lubuntu Linux. It derives from the mainstream Linux, but uses a less demanding GUI called LXDE. You can use several other lightweight versions of Linux in its place, such as LXLE, a derivative of Lubuntu, or Zorin OS, which mimics the look and feel of Windows 7 or Windows XP.
You’ll need to make an installer. You can make a DVD or a USB flash drive as your installer.
To make an installer, first download the .iso file of the Linux distribution you choose to use. You can either download them directly or as a BitTorrent download. Now BitTorrent is notorious as a method of downloading pirate files, but in this case, you can rest assured you’re perfectly legitimate. In fact, you are helping the developers of the Linux distribution if you choose to let your BitTorrent client continue running after you finish your initial download. You’re spreading the word!
Anyway, back to the topic. You’ve finished downloading your .iso file. If you have Windows 7, you have the built-in capability to burn an ISO to a DVD. If you have a Mac, you can use Disk Utility to burn an .iso to a DVD. If you still have Windows XP, you can download and install the free Infrarecorder DVD-burning program.
Now I personally prefer to install Linux distress using DVD-R/W disks. You won’t fill a landfill making DVD’s of old distributions. Just erase the old distro and re-record.
I use USB flash drives to install OS X nowadays. I don’t have to figure with any BIOS screen settings for setting the boot order in OS X. In Windows, you would have to fiddle with the BIOS in most cases to get a USB drive recognized as the new boot drive to start from. It’s up to you.
You’ve made your installer, your BIOS will boot from it, and away you go. Restart the computer by selecting “Restart” from the Start menu or by quickly pressing the hardware restart button.
You should have no trouble with the Lubuntu installer. It’s as easy as the OS X installer. It will ask you if you want to install Linux side-by-side with the existing operating system (Windows, most likely) or wipe out the old system and set up Linux as the sold system. I’ll leave it to you to decide which route you choose to go.
If you keep a rump installation of Windows, you can open it up in Linux through its file manager. This is one of the benefits of Linux, you can use it with Windows. You might want to keep it to rip audio CD’s in iTunes. You might want to run Quicken in it.
After you’ve made your choices, you can wait for Lubuntu to install. In 30 minutes, it’s ready to go. Just restart and eject the installation media.
Installing the Music Software Software
First, you need to run the system updates. Since the developers decided on the Gold Master for this version, they’ve made improvements. You want your system to run with the latest stuff.
So, now for some Linux keyboard shortcuts. Hold down the Control and Alt keys with one hand. Now press the letter T. Up comes a Terminal window!
Now type in sudo apt-get update You’ll see a screenful of text scroll up the screen. When it finishes, you’ll return to your screen prompt.
Second, and this is cool but optional, you can run the music server from your client Mac. You can put the music server out of sight in someplace well-ventilated and cool.
You can use SSH (Secure Shell) to run it from it from afar.
Do that keyboard command of Control+Alt+T to bring up a Terminal. Now enter this command sudo apt-get install ssh
Again, you’ll see a screenful of text scroll up your screen. If the screen asks you whether you want to proceed, type ‘Y’ or ‘yes'
When you return to your command prompt, enter this command ifconfig
You will see a lot of text, but you want this inet addr:
Next to that is your machine’s IP address.
Now for the fun part. Open up your Mac’s Terminal. It’s in Applications>Utilities. Enter this command ssh {your user name on linux}@{Linux IP address}
It’ll look like this ssh thomas@192.168.1.99 Note the space between ssh and the user name. Note that you don’t put spaces between the user name and the IP address.
It should ask you if you want to add the RSA key to a list of trusted ones, Type ‘yes'
Now you can type commands from your Mac and away from the server. This is very cool.
Third, you need to have access to your access to your server from your Mac without typing in commands. A very neat program called netatalk does this.
At a terminal, type in sudo apt-get install netatalk A screenful of text scrolls down your screen. Answer ‘yes’ if you are asked whether to instal the program.
Now this is the most difficult part of the installation. You need to edit a configuration file.
Go back to the Terminal. Type in sudo nano /etc/netatalk/atalkd.conf
You get the nano text editor on your screen with a lot of text displayed.
Scroll all the way to the bottom by pressing the Down arrow key.
Now type in this short line of text eth0
That’s a zero and not an oh at the end.
You should see an icon of a screen appear in your Finder’s Shared section.
If you don’t see it within a minute, click on the Mac’s Finder and press the Command and K keys together. On the command line enter this:
afp://{IP address of Linux server}
An example would be afp://192.168.1.99
See if the icon now appears in your Finder’s Shared section of the SideBar.
Now click on that icon. You should see a folder displayed named the Home folder.
Click on it and you should see folders for various categories of Files. Hmm, it resembles the Mac’s User folder doesn’t it? Yes, it does; because the Mac and Linux have common ancestry in UNIX.
Just drop and drag music files into Music. You can drop these types of files: mp3, m4a, and m4p.
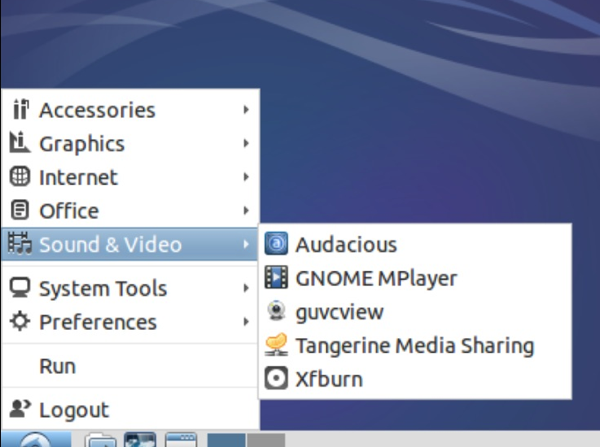
Fourth, time to install the actual Tangerine music server
To install the Tangerine music server, go back to the Terminal. Enter this command sudo apt-get install tangerine
A screenful of text scrolls by. If asked whether to install, type ‘y’ or ‘yes’ as requested.
When you return to the screen prompt, now it’s time to set up Tangerine.
Fifth, setting up Tangerine
On Lubuntu, you’ll find Tangerine under Sound and Video. Click on it and this is your setup screen.
Change the name to suit your fancy.
Set the music source to your Music folder.
Decide if you want to limit access to your music server. Do you want to limit the number of listeners and require them to log in with a password?
Now for some command-line tricks to make life easier.
You will notice that if you add music to the Music folder on the Linux server after you start running Tangerine, it doesn’t automatically pick it up. In fact, some times you click on the Tangerine server in iTunes and see nothing. What do you do?
If you’re allergic to the command line altogether, you can open up Tangerine and change the name of the share. Alternate between “Hot music to listen to” and Cool music to listen to” This forces Tangerine to re-read the music folder. You will see the previous blank music share still displayed in iTunes.
To really clean up the situation, you use the command line. Enter sudo pkill tangerine. The terminal will then ask you for your administrative password, which you created when you set up Linux. Remember, you had to enter it twice?
Well, enter it here and you get temporary root access. When you enter it, you won’t see anything displayed in order to protect your privacy. Press the ENTER key. If you didn’t make a mistake, Linux will shut down Tangerine. The shared music will disappear from iTunes.
So add as much music to the Music folder as you please. Copy it over in the original folders. You don’t have to dump it into your Music folder as one big mess of files. Tangerine will go through your folders and display all your music in iTunes.
Now enter this command sudo tangerine .tangerine & and press the ENTER key. You may have to enter your password again. This command will restart Tangerine
I want to point out the structure of this command.
sudo means you have temporary root access. It comes at the beginning of a command
tangerine is the name of the program you want to run. Note that you put a space between it and sudo and between it and the following command.
.tangerine refers to Tangerine’s configuration file. The period at the front of it means this is ordinarily a hidden file that you can’t see.
& means the command keeps running but it moves to the background. You get control over your terminal back.
I want to thank Isa Raffee for showing me these commands in their Wordpress blog post.
Notes:
Tangerine does not transcode your music. If iTunes won’t play the file format, such as a FLAC file, it won’t work.
I have tested Tangerine with both 32-bit Lubuntu and 64-bit Lubuntu. Both gave the same performance. I have also tested it with the 64-bit Ubuntu derivative running the KDE desktop, Kubuntu. Again, fine performance.
Again, every program I have mentioned is free. So who knows how long Apple will let this work?
I welcome your comments.
Tom Briant
Editor, MacValley Blog
Blog Archive
-
▼
2014
(176)
-
▼
May
(17)
- 10 Coolest Keyboard Shortcuts You Never Knew About...
- Steve Ballmer interested in buying NBA's Clippers?...
- How To Completely Customize Your Mac | Mac|Life
- Rumor: Apple working on ARM-based Mac variants wit...
- Slipping shipping times may support analyst predic...
- Mac OS X software update temporarily broken, likel...
- It's Weekend Wrapup time from Senior Correspondent...
- Use the Finder's tags feature from the keyboard | ...
- The Big List of 111+ Keyboard Shortcuts For The Mo...
- Useful and fun Web site for your chronologic needs
- Mac keyboard shortcuts - Matt Gemmell
- It's time for Senior Correspondent Arnold Woodwort...
- Some Comedy about the Beats Electronics and Apple ...
- Senior Correspondent Arnold Woodworth has a Mother...
- The OS X Friendly Linux Music Server-I try it again
- Beats Audio and Apple? Either the prank of the dec...
- Senior Correspondent Arnold Woodworth has a roundu...
-
▼
May
(17)