The MacValley blog
![]()
Welcome to the MacValley blog, your first stop for all the latest MacValley news and views.
|
The MacValley blog Editor: Tom Briant
|
Labels used in posts
|
To search the blog posts please use the box below
Saturday, July 26, 2014
Senior Correspondent Arnold Woodworth's Weekend Roundup
iPhones have a major security hole that Apple installed on purpose
If you use an iPhone or iPad, your photos, web history, and GPS logs are vulnerable to theft and surveillance via back-door protocols running on all iOS devices, according forensic scientist Jonathan Zdziarski, better known by the hacker moniker "NerveGas."
His conclusion: while iOS 7 security is pretty good overall, it has hidden back doors that could be exploited.
Zdziarski disputed that users can control whether their data is shared. "I don't buy for a minute that these services are intended solely for diagnostics," he said on his blog.
http://qz.com/238275/iphones-have-a-major-security-hole-that-apple-installed-on-purpose/
Five Retail Rules Flagrantly Violated by the Apple Store
http://www.businessweek.com/articles/2014-07-22/five-retail-rules-flagrantly-violated-by-the-apple-store
This author thinks that the Apple – IBM deal is a sign of weakness
http://moneymorning.com/2014/07/24/these-industry-powers-have-never-been-more-scared/
Here’s Why Tim Cook Is Upbeat On iPads Despite Its Shrinking Sales
Cook is not alone in thinking iPads and tablet sales will grow in businesses this year.
http://www.businessinsider.com/tim-cook-ipads-2014-7
Apple's New Mac Software Will Include Little Changes That Make A Big Difference
http://www.businessinsider.com/apple-mac-os-x-yosemite-walkthrough-2014-7
Everything You Ever Wanted To Know About Apple’s OS X Yosemite Beta Preview
http://techcrunch.com/2014/07/23/apple-os-x-yosemite-beta/
Apple’s New Product Hit: the Mac
From a company that coined the phrase “post-PC era,” Apple’s strong Mac sales are showing that its personal computer isn’t ready to be declared dead.
The PC market has slumped in recent years, while smartphone and tablet sales have increased dramatically. Apple has managed to keep its Mac revenue steady, despite the declining overall market, by grabbing share from rivals. Apple said the Mac has outpaced the broader PC industry in 30 of the last 32 quarters.
http://blogs.wsj.com/digits/2014/07/22/apples-new-product-hit-the-mac/
Hackers bypass online security at 34 banks
Hackers can get past two-factor authentication, which requires customers to type in a code sent to their cellphone or inbox to ensure the user is who he or she claims to be, by convincing customers to download a malicious smartphone app.
In typical form, the attack begins with realistic-looking phishing emails that install malware to give hackers control. Then the malware deletes itself, leaving no traces, and users are redirected to malicious servers when using banking websites.
Two-factor authentication, hailed as an essential second gatepost for online accounts, can sometimes prove to be an empty promise.
http://www.marketwatch.com/story/hackers-bypass-online-security-at-34-banks-2014-07-22
Amazon is a company that has divided investors for years. Its relentlessly fast-growing revenues typically translate into relatively diminutive profits because the company reinvests most of its enormous cash-flow into expanding its infrastructure and maintaining low prices
it would be extremely difficult for any competitor to build a viable competing service to Prime-the required investment would be massive, and Prime is just too big to compete with now, and offering too many products. In other words, it's becoming a moat for Amazon.
http://qz.com/237933/amazon-is-building-the-retail-worlds-most-unbreachable-moat-and-its-called-prime/
Nadella tries to fix Microsoft's GM problem: The tech giant's 18,000 job cuts were overdue and unavoidable
Microsoft's purchase of Nokia wasn't overly expensive or a bad idea. It just didn't acknowledge the fact that this race already was over, and Nokia, which was falling behind was bloated itself.
Satya Nadella has made the hard choice to basically end the folly.
http://www.marketwatch.com/story/nadella-tries-to-fix-microsofts-gm-problem-2014-07-17
What the Internet Can See From Your Cat Pictures
If you include more metadata than you have to with your photos — there are tools to scrub that data — don’t be surprised if it’s used online in ways you didn’t expect and can’t fully control.
http://www.nytimes.com/2014/07/23/upshot/what-the-internet-can-see-from-your-cat-pictures.html?emc=edit_ct_20140724&nl=technology&nlid=11893479
Your Facebook ‘cult’ won’t let you quit
If you deactivate your Facebook account, or even just stop posting updates for a couple of weeks, a virtual army – your Facebook friends – will text, email and Tweet, asking what’s wrong and imploring you to come back, says Abby Rodman, a psychotherapist in Boston.
So why do people take umbrage at Facebook deserters? Friending someone creates an unwritten social contract that two people agree to “like” each other’s updates and shower each other with attention, says Cal Newport.
Job-hunters are also under pressure to maintain a social media presence. “Having no Facebook profile would be a little bit weird when applying for a job in marketing, sales, recruitment, or any consumer-facing or business-to-business role,” says Nicole Greenberg
http://www.marketwatch.com/story/facebooks-cult-is-a-win-for-shareholders-2014-07-23
‘Right to be forgotten’ ruling is backfiring, says Data watchdog
Google’s policy of notifying news publishers about links it had removed led to the news publishers flag the articles and give them to a burst of publicity.
http://www.irishtimes.com/business/sectors/technology/right-to-be-forgotten-ruling-is-backfiring-says-data-watchdog-1.1877421
10 things bitcoin won’t tell you
http://www.marketwatch.com/story/10-things-bitcoin-wont-tell-you-2014-07-25
Tinder Is Full of Robot (i.e., FAKE) Prostitutes
What is really going on: Far from being the wild west of the sex trade, Tinder is suffering from a plague of spambots. It is quite possible that at some point recently there really were flesh and blood escorts using Tinder, but the new and ubiquitous ones flooding my stream seem nothing more than artificial profiles.
These were definitely NOT real people. But why the spambots? The answer is incentives of getting people to sign up as members of iHookUp.com.
Through a traffic and lead generation agreement with LoadedCash.com, one can earn ......
What originally seemed like a new frontier for the sex trade turned out to be a fairly simple money making scheme by some enterprising programmers.
http://valleywag.gawker.com/tinder-is-full-of-robot-prostitutes-1610277221/+jparham
http://www.theguardian.com/technology/2014/jul/16/tinder-spam-adult-webcams-fake-prostitutes
The Danger of the Internet of Things
http://www.market-ticker.org/akcs-www?post=229235
17 Apps Every Modern Gentleman Should Have On His Phone
http://www.businessinsider.com/17-apps-for-the-modern-gentleman-2014-7
Sunday, July 20, 2014
Senior Correspondent Arnold Woodworth's Weekend Roundup
Here's A Giant Presentation That Tells You Everything You Need To Know About Apple Right Now
http://www.businessinsider.com/apple-presentation-2014-7
15 Apps For Your iPhone That Are Better Than The Ones Apple Made
http://www.businessinsider.com/15-iphone-apps-better-than-apples-2014-7
11 Tiny Design Features That Show Apple's Insane Attention To Detail
http://www.businessinsider.com/details-that-make-apple-products-unique-2014-7
Apple And IBM Announce Huge Partnership For Large Business Customers
the partnership will play on the strengths of both companies. IBM will use its sales force to sell iPhones and iPads to its network of business customers. IBM will also develop cloud services optimized for iOS, the operating system for iPhones and iPads.
Apple will provide hardware support for devices through a special AppleCare program designed for big businesses buying Apple gadgets in bulk.
While the IBM-Apple partnership may not seem shocking today, it's pretty crazy considering the two companies were mortal enemies some 30 years ago.
http://www.businessinsider.com/apple-ibm-enterprise-partnership-2014-7
The IBM Partnership Makes Apple A Real Enterprise Player In Retail
The author of this article says that the new partnership with IBM will help Apple avoid mistakes that would be very costly to corporate "information tech" departments.
http://www.forbes.com/sites/paularosenblum/2014/07/18/the-ibm-partnership-makes-apple-a-real-enterprise-player-in-retail/
Apple And IBM: Meh
Amusing how this is considered "news."
Look, let's get to the bottom line right up front: IBM has no mobile strategy of any sort. Period.
So this isn't a "partnership" at all; it's essentially a sales agreement with Apple's products.
http://www.market-ticker.org/akcs-www?post=229198
In retrospect, the historical partnerships between Apple and IBM didn't have a very good track record. Taligent and Kaleida were total failures, while PowerPC failed to keep up with the pace of the greater market. IBM Lotus Notes and Symphony did not exactly transform the industry on any platform.
But today's Apple and IBM share little in common with their previous incarnations in the 1990s.
the two described "exclusive" plans to work together to "transform enterprise mobility through a new class of business apps."
The language both companies use in describing their partnership indicates that it is not merely an effort to sell a few companies an extra thousand iPads. Apple and IBM have big goals in mind.
http://appleinsider.com/articles/14/07/17/what-apple-inc-gets-from-its-new-ios-partnership-with-ibm
Apple Starts Encrypting All iCloud Email
http://www.tomsguide.com/us/apple-encrypt-icloud-email,news-19184.html
http://appleinsider.com/articles/14/07/16/apple-implements-transit-encryption-for-icloud-email-to-prevent-snooping
I Ditched My iPhone For A Samsung Galaxy S5 And Was Blown Away By What I Was Missing With Apple
http://www.businessinsider.com/iphone-compared-to-samsung-galaxy-s5-2014-7
Construction of Apple's Future Headquarters Progresses:
Photos of Apple Campus 2 construction site show 'underground tunnels,' continued progress
http://appleinsider.com/articles/14/07/17/photos-of-apple-campus-2-construction-site-show-underground-tunnels-continued-progress
What Apple has in common with Britain’s top spy agency
Headquarters shaped like doughnuts (or flying saucers). As soon as Apple completes construction.
http://venturebeat.com/2014/07/18/what-apple-has-in-common-with-britains-top-spy-agency/
I'm 22 Years Old, And I Grew Up Without The Internet
http://www.businessinsider.com/my-life-growing-up-without-internet-2014-7
The Science Behind Why Tinder Is So Addictive
By taking all the pesky guesswork out of the flirting game, Tinder has made it so gauging romantic or even just sexual interest is as simple as a split-second thumb swipe. Whether or not that’s a good or bad thing is up for debate.
http://www.businessinsider.com/why-tinder-is-so-addictive-2014-7
The 12 Most Popular Free Online Courses For Professionals
http://www.businessinsider.com/free-online-courses-for-professionals-2014-7
Beethoven Used This Strategy To Keep Creative Ideas Flowing
1) Stop before you are empty (i.e., leave a little bit undone at the end of each day)
2) Define your goals the night before
3) Step away from problems midday with a contemplative walk
It might not turn you into a famous writer, but see if it doesn’t help with your creative process.
http://www.businessinsider.com/beethovens-creative-strategy-2014-7
The Internet is in many ways a blessing and a curse for investors. Arguably one of the biggest benefits is the speed with which information flows, and the sheer amount of it which is accessible with the click of a button. Too much of something, however, can be a very detrimental thing.
Consider that the more information and data we are inundated with, the less we focus on what matters.
What matters is not the here and now when it comes to wealth generation, but probabilities over longer samples in history.
What matters is not looking at every single bit of information that people present when it comes to stocks and bonds, but the few variables that explain the bulk of asset class movement.
http://www.marketwatch.com/story/are-crash-conditions-growing-or-fading-2014-07-14
China’s bevy of supercomputers goes unused
China has built the second largest collection of supercomputers after the U.S., including the world’s fastest supercomputer, the Tianhe-2.
But it seems a lot of these massive machines, usually made with large government investment, lie idle ...... due to fundamental defects in China’s traditional bureaucratic management system.
China’s supercomputers have a very low utilization rate
http://www.marketwatch.com/story/chinas-bevy-of-supercomputers-goes-unused-2014-07-15
Ireland Central Bank Official Admits Bitcoin’s Disruptive Potential
"Virtual and digital currencies can challenge the sovereignty of states,” says Gareth Murphy, senior Central Bank of Ireland official.
Bitcoin undermines a central bank's ability on matters such as economic analysis, data collection, supervision, policy formation, enforcement and resolution, so these sort of implications can't be overlooked.
http://cointelegraph.com/news/112015/ireland-central-bank-official-admits-bitcoins-disruptive-potential
How Bitcoin Can and Will Disrupt the Financial System
The recent emergence of crypto-currencies has the potential to change the way people buy and sell throughout the world.
It is not until today that people have a new method to bypass financial intermediaries and transact directly with one another.
Crypto-currencies remove the middleman and make the transaction more efficient.
This disruptive technology can and will transform our economy.
http://www.visualcapitalist.com/how-bitcoin-can-and-will-disrupt-financial-system/
Saturday, July 19, 2014
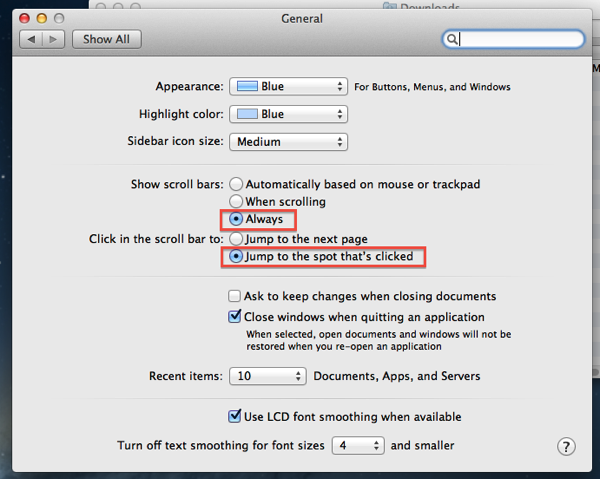
Off with the pants-Scrollbar preference tips from a blogger who's NOT wearing pants tonight
I saw a complaint that OS X 10.8 (and by extension, 10.9) do not display the Scroll Bars at all times.)
In a word, well made up word, zschau-WHAT? Isn’t this changeable in the System Preferences? Wouldn’t a quick trip to Google find a solution?
Yes, and thanks to the good people at OS X Daily, they have a fix for it right here.
Using my OS X 10.8.2 test partition, I tried out myself and this is what happened.
This is what the Finder in 10.8.2 looked like before. Note NO Scrollbars either on the left side and on the bottom.
Why do they act this way? Because General Preferences in System Preferences is set that out of the freakin’ box/download, that’s why!
So a few changes are made to General Preferences as shown below. The Scroll Bars are turned to always on.
And now we have scroll bars on! All the time!
Tom Briant
Editor, MacValley Voice
Pro Tips from a blogger wearing pants-Use Command + Tab to switch between open Mac programs and something similar for Windows users, too
It has come to my attention that some of you don’t know how to move between open programs on either the Mac or Windows. So I’m going to teach you how to do this.
The two people I taught this to have already paid for your lesson by either cooking me dinner or buying lunch and dessert. Thumbs up to Ernie’s Taco House in North Hollywood!
To get to the topic, if you want to switch between open programs on your Mac or Windows machines, do this:
On a Mac, hold down the Command/Apple key with your left thumb and use your forefinger on the Tab key to bring up the following screen:
Successive taps of your forefinger while keeping your thumb depressing the Command key move the focus to each program’s icon moving rightward.
Hold down the Shift key in addition to the Command and Tab key and the focus moves left-ward.
For Windows 95 through 8, hold down the Alt key with your left thumb and press the Tab key with your forefinger.
You will see the same bar in the middle of your screen as you would with OS X.
I took these Mac screenshots with OS X’s utility Grab. You’ll find it in the Utilities folder within Applications. It’s been there since 10.1 at least. I used the Timed Screenshot.
For Windows, I used the multi-function IrfanView utility. Your homework assignment is to Google “Irfanview” and see how many hits you get. Trust me, for a Windows user it’s indispensable. And it’s FREE! Even if you’re a Mac user who runs Windows XP under Virtual Box, you should check this out. It’s that great a program.
Tom Briant
Editor, MacValley Blog
Senior Correspondent Arnold Woodworth's Weekend posting
Editor’s apology-I’m running late on running these articles. Arnold sent them to them but I got distracted. So here are last week’s postings.
Tom Briant
Editor, MacValley Blog
National Federation of the Blind says "Apple has done more for accessibility than any other company"
http://appleinsider.com/articles/14/07/12/national-federation-of-the-blind-says-apple-has-done-more-for-accessibility-than-any-other-company
Jury gives full defense verdict to Apple, swats down $511M patent demand
Apple is 2-0 against "patent trolls" this year, and it faces a third trial soon.
http://arstechnica.com/tech-policy/2014/07/jury-gives-full-defense-verdict-to-apple-swats-down-511m-patent-demand/
China calls Apple’s iPhone a security threat
App could expose ‘state secrets’, state media says
China’s influential state broadcaster called a location-tracking function of Apple Inc.’s iPhone a “national security concern” on Friday, in the latest backlash against U.S. technology firms.
Look at the reader comments to this story. A few of them are very good.
http://www.marketwatch.com/story/china-calls-apples-iphone-a-security-threat-2014-07-11-71033435
Apple Denies China's Accusation The iPhone Is A 'Threat To National Security'
Apple explained in its message that the location data is stored only on each phone, not on Apple's servers, and that all of it is encrypted. The company also tries to quash fears that it's working with the government to spy on iPhone owners.
http://www.businessinsider.com/apple-china-data-location-tracking-claims-2014-7
Apple launched a blog Friday aimed at developers for its new Swift programming language.
The move marks a change for notoriously secretive Apple
http://blogs.marketwatch.com/thetell/2014/07/11/apple-launches-blog/
Apple's Swift blog shows how important the new language is
Regardless of the motivations behind it, this blog is great news. Apple’s attitude towards developers has improved by leaps and bounds.
http://www.macworld.com/article/2452694/apple-launches-a-new-swift-blog-signaling-languages-importance.html
Here's What Happens When Kids Today See The Original Game Boy For The First Time
http://www.businessinsider.com/kids-today-react-to-original-game-boy-2014-7
It's Becoming Clear Just How Vast The Censorship Of Google Is Going To Be
http://www.businessinsider.com/google-right-to-be-forgotten-censorship-2014-7
Google and security? You're kidding.
The Google Play "ecosystem" has been diametrically on the other side of security forever.
Security is a process, not a product. Examining apps before approving them requires time, and time is the enemy when your first, foremost and only concern is making as much money as possible and vacuuming up as much information as possible.
Android (and IOS, for that matter) are diametrically opposed to enterprise-level (not to mention personal) security. They both wish to own and process the data you have on your device, tying them inexorably to the publisher's services. This is how they make money, and as such expecting otherwise is simply foolish.
Many enterprise users will find BlackBerry's "Balance" to be exactly what the doctor ordered. But -- BlackBerry is missing a few things.
if you give enterprise users a way to carry only one device yet give up nothing in terms of both personal use and enterprise security you will have a huge win.
Nobody does it today, but BlackBerry is the closest
http://www.market-ticker.org/akcs-www?post=229184
Hackers know who is shipping what, and to where
How malware is infecting shipping scanners
Seven shipping companies across continents have discovered malware in their scanners that siphoned their financial, customer and other data to a Chinese botnet.
http://www.marketwatch.com/story/how-hackers-are-infecting-shipping-scanners-2014-07-10
The CIA Is Trying Too Hard To Be Cute On Twitter
The U.S. Central Intelligence Agency ramped up its attempts at humor Monday with a series of posts fired off on its new Twitter account
http://www.businessinsider.com/the-cia-is-trying-too-hard-to-be-cute-on-twitter-2014-7
Sunday, July 13, 2014
MacValley's opinion on the rumored iWatch-it's coming and I don't know when
Quite a few pixels have been wasted on the topic of when will Apple bring forth the rumored iWatch?
Various “analysts” parse the public available information on Apple’s new hires. such as someone from Tag Heuer. Another day, it’s people let go by Nike from their fitness band project.
Right off the top of my head I would say that Apple does intend to bring out some sort of wearable device that fits around your wrist. As to when they will bring it out, I don’t know and I expect my ignorance is shared across the range of journalists and bloggers. (Note; for this article, I was wearing pants, therefore I am a journalist)
I am mildly curious about Apple’s plans for wearable devices. Surely this would fall into both Jony Ive’s and Angela Ahrendt’s shops? Will they offer a model to monitor various health parameters? Will they offer a watch that will become the hot item for fashionistas to wear in the fall of 2014 or spring of 2015? Will it be the same device or two different items? Separate styles for men and women? What about colors?
I will leave coverage of the iWatch to my fashion-conscious colleges. Elena-Beth? Cristael? What do you have to say?
Happily wearing my Big Lots! watch,
Tom Briant
Editor MacValley Blog
Sunday, July 6, 2014
LibreOffice for Mac-Certainly a StopGap, Possibly a Replacement
A member of MacValley recently asked me to recommend a replacement for MS Office 2004. They have a lot of old documents in MS Office 2004 formats, which would cover MS Office 97 for Windows and MS Office 98 for Mac, through MS Office 2003 for Windows and MS Office 2004 for Mac.
What could I recommend as a replacement for MS Office 2004, which upgrading from OS X 10.6.8 to 10.8.5 had rendered inoperative? I told them to go with LibreOffice 4.
I have read the reviews of LibreOffice on-line at PCMag.com and other sites. What it comes down to is this:
LibreOffice is free to use. FREE! Make a donation if you feel it helped you out in whatever amount you want to make.
The User Interface is not that good. It’s stuck back in the ‘90s at worst and MS Office 2007 at best. It’s not as good as MS Office 2013 for Windows and the latest version of iWork. Then again, some users detest the Ribbon interface introduced by Microsoft.
Its big advantage over the competition is that it reads many otherwise obsolete formats, such as WordPerfect for DOS, Windows, and Mac. It reads Appleworks/Clarisworks word processing documents.
As a stand-alone office suite, it is the best solution for someone who right now needs to spend the money that would go for iWorks or Office 2011 on food, gas, and rent. You might want to test it out versus iWorks for the Cloud or Google Drive. You’ll have to store your works up in the cloud, though. Is that a problem?
One last note. Version 4.1.6 is the 32-bit version which runs on both 10.6.8 and 10.9.4. Version 4.2.5.2 is a 64-bit version that requires 10.8 at a minimum.
The interface on versions 4.2.5 shows some upgrades over the old interface in 4.1.6. You can try them both and make a selection.
Tom Briant
Editor, Macvalley Blog
MS Office 2004 rendered inoperative and I've got a TON of stuff I use with it! Here's what to do!
A MacValley member brought me back to Earth with their problem. A problem that many people will face as they finally upgrade from 10.6.8 to 10.8, 10.9, and 10.10. They have a machine that runs 10.6.8 now and they want to upgrade to a recent version of OS X.
The problem is this: They’ve got programs and stuff based on the old PowerPC CPU. In today’s case, it was their treasured Office 2004. Oh, no, they can’t access spreadsheets!
The answer is simple: Backup your existing partition, then download and install LibreOffice 4. Then upgrade to OS X 10.8 or 10.9.
You will need three items.
An external hard drive partition with enough space to back up the main hard drive. If you don’t have a hard drive handy, you can buy a USB hard drive with 1 TB capacity for under $100 at Frys or Costco or Best Buy.
A program to clone your existing hard drive. I suggest Super-Duper, because it’s FREE if you just want to back up the whole drive after wiping out the target drive. It’s $27.95 if you want the additional features. I recommend you get it.
If you have Carbon Copy Cloner or another cloning program, that will work just as well. But you need to clone your hard drive.So get to work.
The third part of this equation is for you to download and install LibreOffice 4. It’s a free program, but donations are welcome.
LibreOffice 4 comes from an international effort, headquartered in Germany, to develop an alternative to MS Office. They have versions for Windows and Linux, too. In fact, most Linux distributions include LibreOffice as part of their installation.
Back to the Problem at Hand
“I don’t see any USB 2.0 drives or Firewire 400 drives on the shelves. What do I do?”
I’m assuming you see lots of USB 3.0 drives. Don’t worry, USB 3.0 is backwards compatible with USB 2.0. Just plug the USB 3.0 cable into your Mac’s USB 2.0 ports. It won’t run as fast as USB 3.0, but at the slower USB 2.0 speed.
If you want to buy a Firewire hard drive, you’ll probably find Firewire 800 hard drives on the shelves. Don’t worry, if you get an adaptor cable for Firewire 800 to Firewire 400, they’ll work just fine. You’ll find the cables at Frys.
“What’s involved in cloning a hard drive? Why can’t I just drag and drop from my old drive to my new drive?"
Unfortunately, turning a new empty drive into the bootable clone of your current drive is more complicated than just dragging and dropping folders. You have to set up disk and folder permissions, which gets complicated. Best to let a cloning program do it for you.
I recommend Super-Duper because I know it works and for the purposes of this article, it’s free to use. Comments are welcome regarding other cloning programs. But I’m going to show you how to use Super-Duper.
Installing Super-Duper is simple. First, you go to their Web site, Shirt-Pocket Software and download the .dmg file. I assume you use OS X 10.6.8 Snow Leopard, so you can use the latest version of Super-Duper, 2.7.2.
Double-click on the Super-Duper! .dmg file. You’ll see this screen pop up
This is a license agreement. Essentially it means that if you’d like to use any of Bruce B. Lacey’s computer code in your own program, you have to ask him first, Politely. Otherwise, he can sue your pants off and win.
If you just plan to use Super-Duper! to clone your hard drive and do not want to infringe on Mr. Lacey’s intellectual property, then click on the “Agree” button.
This brings you to the second window, which shows the Super-Duper! app, the introductory ReadMe document which you read with TextEdit, and a link to the full Super-Duper! manual in PDF format. Mr. Lacey has a copy within the program for your reference. Just go to the Help menu.
To install Super-Duper!, follow the simple instructions. Drag it to the Applications folder and run!
Running Super-Duper!
You want to set up Super-Duper so that the screen looks like this:
For “Copy” select your main Macintosh hard drive, probably called Macintosh HD. You want to clone this drive onto —> the
“To” drive, which is the drive you bought for this purpose.
You want to set up the “Options” so that the drive fixes your disk permissions on your Macintosh HD before you start cloning.
After you finish cloning, you want to set up the end game. Do you want the Mac to shut down? Do you want to boot from the newly cloned drive? You have several choices.
How do I change from my Macintosh drive to this external “My Clone” drive?
You have two ways to change between the drives or partitions you start from:
The easiest way for you to change drives is to use the Startup Disk system preference in your System Preferences
Just go to Startup Disk and select the Startup Disk you want. I have a lot of startup disks that I can use with my Mac.
(No, I can’t boot up on my current Mac with 10.5.8 and 10.4.11. I use those partitions with my old 2006 MacBook)
The second method is to restart your Mac and hold down the Option key. You’ll see a display of all the bootable drives attached to it, including the otherwise hidden Restore partition.
And one of those drives would be your “My Clone” drive after you’ve completed formatting it and cloning it.
Now a word of warning!.
The drive you bought at Frys or Costco or Best Buy is usually formatted to use with a Windows machine.
Your Macintosh can read this drive, but it can’t write to it. Note the red oval at the bottom. You can only read from this drive. You need to reformat it after you copy any information on it to your Mac.
Reformatting a Windows formatted external hard drive for your Macintosh
To format your external hard drive, you use Disk Utility. Here is my latest acquisition, a 1.5 Tb Seagate hard drive which I will show you how to format for use in cloning your Mac hard drive.
The format is MS-DOS (FAT32) and if you look at the very bottom on the right, you’ll see the Partition Map Scheme is Master Boot Record (MBR).
Now Disk Utility says this partition can’t be modified. But I’ll show you how to modify it; change the Snow Leopard’s spots to Maverick’s waves.
For this demonstration, I’ll assume you just want the whole disk available to you. No second or third partitions to complicate matters.
So you’ll get a 1.5 TB drive in Mac HFS+ format and with a GUID Partition Map Scheme from a Windows formatted drive.
Step 1. Change the partitions!
To modify the layout, or partitions, of the hard drive, go to the double-head arrow at the right-hand edge of the box that says, “Partition Layout”. You’re going to change from the current layout to another one. You can choose from 1 to 16 partitions
In this case, you’ll go from the current, 1 partition layout, to a new 1 partition layout. Simple, isn’t it? You simply have to say, “I’m changing everything by using the exact same partition scheme as was previously used."
What have you changed by going from the Current partition scheme to the new 1 partition scheme? You have changed the name of the partition from “Windows” to “Untitled 1"
And you have opened the door for changes to the hard disk format and partition map scheme.
Change the Partition Map Scheme!
Don’t forget to change the Partition Map Scheme under “Options”
“Options” is a button just below the partition map display. Click on it and you’ll see the following.
Note that you have three choices. Right now, your Windows hard drive is set at Master Boot Record, the MS-DOS/NTFS standard. You don’t want that! You want GUID so that you can start up an Intel-based Mac.
Click on the OK button and you’ve set the correct partition map scheme for OS X.
But you still haven’t set the disk format yet. So let’s go to the Format Line.
Hmm, it’s still at MS-DOS (FAT). You need to change this. Click on the double-headed arrow at the right-end side.
You see that MS-DOS (FAT) is checked off. You want to click on the top selection, which is Mac OS Extended (Journaled).
Almost there! Now just add a name to your drive, such as “My Clone”, hit the Apply button (highlighted at the lower right-hand corner) and your drive will be prepared for you.
You can clone your Mac’s internal hard drive to the external hard drive.
So go back to the instructions on using Super-Duper!, clone your hard drive, and fix dinner. Cloning a drive takes some time.
My next piece will introduce LibreOffice 4 to you. It’s your substitute for MS Office 2004 for the time being.
Tom Briant
Editor, MacValley Blog
Sunday Roundup by Senior Correspondent Arnold Woodworth
iPad Used As Medical Device, Huge Success For Apple In Healthcare
An iPad can also be used as a medical device itself. Although it seems unbelievable, it's true. An iPad coupled with a specially designed attachment can work as a state-of-the-art MS (multiple sclerosis) assessment tool.
http://seekingalpha.com/article/2300005-ipad-used-as-medical-device-huge-success-for-apple-in-healthcare
WOZ: Samsung Galaxy Gear Is 'Worthless'
http://www.businessinsider.com/woz-samsung-galaxy-gear-is-worthless-2014-7
The first phones offered by Apple's low-price competitors were cheap because they were crappy.
In the past year, however, the quality of low-priced phones has improved dramatically, to the point where the design and specs of some of these phones, as well as the religious devotion of some of their brand fans, has come to rival that of Apple.
If Apple is ever forced to reduce its prices to compete with the likes of Xiaomi—or if any would-be full-priced iPhone buyers are ever seduced by the far more attractive prices offered by the likes of Xiaomi—Apple's profit is going to tank.
http://www.businessinsider.com/xiaomi-phone-sales-2014-7
The Reign Of Windows At Work 'Is Coming To An End' And Macs Are Rising Fast
http://www.businessinsider.com/vmware-windows-is-coming-to-an-end-2014-7
Apple Fast Facts
Thirty years of the Macintosh
A good summary of Apple and Mac history
http://edition.cnn.com/2014/07/01/business/apple-fast-facts/
Four biggest long term threats to the Internet
Interference by governments
Surveillance programs will erode trust
Commercial pressures will derail the open structure
the problem of finding interesting and meaningful content when you want it
http://blogs.marketwatch.com/thetell/2014/07/03/four-biggest-threats-to-the-internet-pew-study-looks-ahead-to-2025/
Sneaky malware lurks on your computer until you log into your bank
The new strain starts with an old tactic: Spam. Messages detail financial transactions and include a link, but instead of luring users to phony websites to trick them into typing their banking credentials, the malware stealthily injects malicious code into the browser so it can later detect when the customer is banking online.
Last year saw a million new strains of banking malware, double the prior year's volume.
http://www.marketwatch.com/story/sneaky-malware-lurks-on-your-computer-until-you-log-into-your-bank-2014-07-02
A Bright Side to Facebook’s Experiments on Its Users
Facebook’s disclosure last week that it had tinkered with about 700,000 users’ news feeds as part of a psychology experiment conducted in 2012 inadvertently laid bare what too few tech firms acknowledge: that they possess vast powers to closely monitor, test and even shape our behavior, often while we’re in the dark about their capabilities.
The publication of the study, which found that showing people slightly happier messages in their feeds caused them to post happier updates, and sadder messages prompted sadder updates, ignited a torrent of outrage from people who found it creepy that Facebook would play with unsuspecting users’ emotions.
Studying how we use social media may provide important insights into some of the deepest mysteries of human behavior.
It is only by understanding the power of social media that we can begin to defend against its worst potential abuses.
if every study showing Facebook’s power is greeted with an outcry over its power, Facebook and other sites won’t disclose any research into how they work. And isn’t it better to know their strength, and try to defend against it, than to never find out at all?
http://www.nytimes.com/2014/07/03/technology/personaltech/the-bright-side-of-facebooks-social-experiments-on-users.html?emc=edit_ct_20140703&nl=technology&nlid=11893479
Swear Off Social Media, for Good or Just for Now
Your profile includes not only your posts, photos, videos and other valuable digital trinkets, but also a detailed history of everything you have ever done on Facebook. You will see ads you have clicked, how you are being targeted, every time you have logged into Facebook and from which IP addresses, the facial recognition data Facebook uses to recognize you in pictures, and quite a lot more.
That will most likely rush you toward the Delete button. Once you request deletion, your data may hang around on Facebook’s servers for about 90 days and then, Facebook assures me, will be gone forever.
http://www.nytimes.com/2014/07/03/technology/personaltech/swear-off-social-media-forever-or-just-for-now.html?emc=edit_ct_20140703&nl=technology&nlid=11893479
How to Digitally Avoid Taking It to the Grave
So how do you make sure all that information — protected by who knows how many passwords — is handled the way you would like after you’re gone? Two words: Plan ahead.
While the legal issues are being untangled you can plan ahead.
http://www.nytimes.com/2014/07/03/technology/personaltech/how-to-digitally-avoid-taking-it-to-the-grave.html?emc=edit_ct_20140703&nl=technology&nlid=11893479
Google Deleted The Listing Of A Negative Blog Post About Merrill Lynch's Former CEO
http://www.businessinsider.com/google-deletes-article-merril-lynch-ceo-2014-7
Google Is Being Forced To Censor The History Of Merrill Lynch — And That Should Terrify You
The European Union's new law giving people a "right to be forgotten," which requires Google to remove links to information about them, is having exactly the effect its critics predicted: It is censoring the internet.
http://www.businessinsider.com/google-merrill-lynch-and-the-right-to-be-forgotten-2014-7
British Media Cry Foul After Google Removes 'Forgotten' Search Links
http://www.nbcnews.com/tech/internet/british-media-cry-foul-after-google-removes-forgotten-search-links-n147811
Blog Archive
-
▼
2014
(176)
-
▼
July
(10)
- Senior Correspondent Arnold Woodworth's Weekend R...
- Senior Correspondent Arnold Woodworth's Weekend Ro...
- Off with the pants-Scrollbar preference tips from ...
- Pro Tips from a blogger wearing pants-Use Command ...
- Senior Correspondent Arnold Woodworth's Weekend po...
- Apple's first iBeacon hardware revealed in FCC app...
- MacValley's opinion on the rumored iWatch-it's co...
- LibreOffice for Mac-Certainly a StopGap, Possibly ...
- MS Office 2004 rendered inoperative and I've got a...
- Sunday Roundup by Senior Correspondent Arnold Wood...
-
▼
July
(10)